The main premise of this paper is that strict bureaucratic structures, inadequate finances, lack of coordination, reluctance to share intelligence information, fragmentation as opposed to integration, and a lack of accountability remain as the primary indicators of gaps in the US homeland security framework. Despite the mandate of the DHS to help coordinate the efforts of different agencies to combat threats to the security of the country, there is still a lack of interconnectedness between the different agencies (both domestic and international) which prevents coordinated efforts from being properly implemented.
This study examined the factors that contributed to these issues and what methods could be implemented in order to mitigate them in the future. This examination is done under the framework of possible challenges that the DHS will face in light of these issues in correlation with the growing security threats that fall under the mandate of the DHS. The research paper focused on current homeland security issues within the country with a specific focus on the issue of domestic terrorism, how insufficient information sharing, overlapping responsibilities, differing organizational cultures and the current bureaucratized system prevent this security issue from being addressed properly and what methods could be implemented in order to resolve such a problem.
Introduction
The main premise of this paper is that strict bureaucratic structures, inadequate finances, lack of coordination, reluctance to share intelligence information, fragmentation as opposed to integration, and a lack of accountability remain as the primary indicators of gaps in the US homeland security framework. Despite the mandate of the DHS to help coordinate the efforts of different agencies to combat threats to the security of the country, there is still a lack of interconnectedness and cooperation between the different agencies (both domestic and international) which prevents coordinated efforts from being properly implemented to counter terrorist threats both within the U.S. and abroad.
Following the glaring terrorist attacks on September 11, 2001, homeland security became a key national concern. Law enforcement bodies and their respective roles changed at the federal, state, and local levels. The United States’ Congress responded to the attacks by enacting the U.S. Patriot Act, which sought to restructure the federal, state, and local bureaucracies coupled with disseminating powers to law enforcement bodies across various agency departments (Davis 2010, 44). Even though most of the traditional security policies changed drastically, law enforcement personnel have yet to understand how to adapt to these new roles and powers towards curbing terrorism. In many respects, many people may perceive Homeland Security as a recent policy area developed to react to the terrorist attacks of September 11. However, it is not a new idea since the U.S. government has been dealing with domestic invasions for a long time. In addition, much attention since the World War I has been given to safeguarding the home front from internal and external enemies. However, the concept of homeland security shaped as an internal policy after the September 11 incident.
Several national intelligence issues continue to pose a threat to the future of the Department of the Homeland Security (DHS) including strict bureaucratic structures, inadequate finances, lack of coordination, reluctance to share intelligence information, fragmentation as opposed to integration, and lack of accountability (Jenkins, Liepman, and Willis 2014, 19). In addressing these issues, this research paper will answer the question of what sort of challenges will the DHS continue to face in the future. These areas will continue to pose challenges because the decision makers seem to be content with the existing bureaucratic organization. Second, the same bureaucratic leadership is tasked with the allocation of finances meaning that considerable time will be wasted while trying to distribute funds to the security bodies. Furthermore, due to the bureaucratic systems, information sharing is highly restricted to a few people, thus leading to mistrust and further fragmentation of intelligence bodies (Goldstein 2013, 11).
The most prominent future intelligence challenges encountering the DHS are attributable to the September 11 attacks. Most notably, the immediate response issued by the George Bush administration was an enforcement of strict bureaucratic systems across the national intelligence community. This approach did not solve the problem, but it created differences since many workers were demoralized due to working under highly bureaucratized structures. This system has been reflected in the current Obama administration not only in the security systems, but also in other departments that influence the performance of the security agencies. Currently, the process of recruitment, training, and firing of workers is strictly bureaucratized. For instance, the incumbent Secret Service Permanent Chief, Joseph Clancy, has often expressed his regrets over the complex system deterring him to take swift actions to security agents and other officers who engage in mischievous and unacceptable behaviors (Rogers 2014, 337). Following the intensive consultations in decision-making, achieving timely interventions has been in vain. In addition, lack of adequate finance has led to poor service delivery and yet the government looks reluctant to utilize soft power to mitigate this issue. The challenge to homeland security is addressing the aforementioned issues that have been identified. Now the question is why is there a lack of cooperation when obviously it is in the best interests of the parties involved to cooperate to prevent terrorist activities from occurring?
Statement of the Problem
Insufficient information sharing by key federal and international entities, overlapping responsibilities, differing organizational cultures and a highly bureaucratized system remain as the primary indicators of gaps in the US homeland security framework. Despite the mandate of the DHS to help coordinate the efforts of different agencies to combat threats to the security of the country, there is still a lack of interconnectedness between the different agencies which prevents coordinated efforts from being properly accomplished. It is based on this that this study will examine the factors that contribute to these issues and what methods could be implemented in order to mitigate them in the future. This examination is done under the framework of possible challenges that the DHS will face in light of these issues in correlation with the growing security threats that fall under the mandate of the DHS. The research will thus focus on current security issues within the country with a specific focus on the issue of domestic terrorism, how insufficient information sharing, overlapping responsibilities, differing organizational cultures and the current bureaucratized system prevent this security issue from being addressed properly and what methods could be implemented in order to resolve such a problem.
Literature Review
Introduction to the Literature Review
Even before the September 11 attacks, intelligence analysts had explored the risks and threats of terrorism in a bid to fill the gaps that persisted within the US security system (Hymans 2006, 457). The experts repeatedly identified the lack of cooperation and poor coordination as the eminent concern amongst the several bodies linked to the Department of Homeland Security. Prior to these attacks, the law enforcement system was divided and bureaucratized; for example, the CIA addressed foreign threats while the FBI handled internal threats. This fragmentation encouraged division and different versions of intelligence operations. In most cases, the National Security Agency (NSA) dealt with similar problems, thus resulting in an overlap in esponsibilities. Before the attacks, the US government lacked a clear framework for pulling its intelligence expertise together to offer protection against terrorism. Insufficient information sharing by key federal entities remains the primary indicator of the security gaps in the US.
Challenges Facing the Department of Homeland Security at the Present
Threats
One of the growing threats that the DHS is facing at the present is the issue of domestic terrorism brought about by international terror organizations such as ISIS. As seen in the article “ISIS and the Lonely Young American” in the June 27, 2015 issue of the New York Times, ISIS has been utilizing the medium of the internet in order to induct people into their jihadist mentality. The author of the article, Rukmini Callimachijune, stated that as of January 2015 nearly 100 Americans had left the U.S. in order to join the cause of ISIS in Syria and Iraq. This number represents just a small portion of the nearly 4,000 westerners that have supposedly been recruited through the internet in order to become part of the “war effort”. Recruitment of local civilians within the U.S. often entails the use of social networking sites such as Twitter and Facebook in order to get close to potential converts and slowly induct them into the jihadist mentality.
This creates a significant homeland security issue since this in effect generates threats within the U.S. that the department cannot keep track of. One of the main methods of preventing terrorists from setting foot in the U.S. has been through strict screening procedures involving incoming passengers into the country. This, combined with an international “no fly list” and subsequent efforts to identify known terrorists, has enabled the U.S. to protect its borders from terrorist threats in a post 9-11 security environment (Dickens 2007, 2179). However, these measures cannot prevent the development of internal security threats that may result in the creation of radical jihadists out of everyday Americans. Evidence of this can be seen in the case of the London Bombings that occurred on July 7, 2005 that were perpetrated by four Islamist suicide bombers who were citizens of the UK. Further examination of the motives behind the bombers revealed that they ascribed to views that were being promoted by radical Islam and had connections to terrorist groups in the Middle East (Dickens 2007, 2180). This situation shows that recruitment and the subsequent radicalization of local citizens towards committing terrorist acts is a real threat to the continued domestic security of the U.S.
Monitoring and preventing these threats falls under the domain of the DHS; however, there are several problems that prevent the department from doing so effectively. The first of these issues is the incapability of the department to monitor all incoming data traffic into the U.S. that can be classified as originating from terrorist recruiters (Light 2007, 175). On average the internet traffic entering into the U.S. is staggering with social networks such as Facebook and Twitter often having millions of users and hundreds of millions of different messages and files sent on a daily basis (Light 2007, 175). While it is true that some methods of “filtering out” the messages can be done by focusing on data that specifically comes from areas that have been identified as having elements of radical Islam, the New York Times article that was mentioned showed that recruiters can also come from supposedly “safe” regions such as the UK.
Not only that, there are also problems in relation to the necessary personnel, equipment and expertise needed to examine millions of messages and determine their origin, who these individuals are and mark them for further investigation and observation (Light 2007, 176). Lastly, there are also issues in relation to the DHS overstepping its mandate by violating the privacy of millions of Americans by observing their incoming and outgoing data traffic. What these problems show is the necessity of combining the capability of identifying data traffic that is specifically geared towards recruiting people towards radical Islam, determining who has been contacted within the U.S. and by whom and putting into place the necessary actions to observe such individuals and mitigate possible threats to the domestic security of the U.S. before they occur (Light 2007, 178). Such activities entail cooperation between multiple agencies such as:
- the NSA for data identification
- the FBI for observing potential local threats in the form of radicalized American citizens
- the CIA to track the individuals in foreign countries that are attempting to radicalize local Americans
- Lastly the local police whose job is to observe and intervene once it has been determined that the communication between them and the recruiters has reached a point that it may compromise the domestic security of the U.S.
While the utilization of such a strategy may seem obvious, there are issues when it comes to coordination between the different agencies that create significant challenges when it comes to putting such a strategy into effect (Ritchey 2011, 38). It is based on this that the next section will focus on issues related to coordination across different agencies.
Coordination
Based on the work of Gorman (2004), it was noted that the reason behind the lack of inter-department and inter-agency cooperation involving the DHS stemmed from fragmentation as opposed to integration when it came to implementing security operations as well as a distinct reluctance to share information (Gorman 2004, 696). From a homeland security perspective, it makes sense that the different departments that are in charge of ensuring the safety of a country’s citizens should work together in order to pool resources and knowledge in order to better counter potential threats. However, there is a significant difference between perspectives and actual practice wherein present day relations between different agencies and departments are severely lacking when it comes to cooperation, collaboration and information sharing.
McCreight (2009) went deeper into investigating this issue by stating that the present day problem has its origins in the Deutsch and Coleman theory of cooperation and competition. This theory explains that when it comes to situations that require negotiation, both parties have the option of cooperation or competition wherein the outcome of the conflict between the two parties is either of the aforementioned factors (McCreight 2009, 4). McCreight takes this even further by explaining that, ordinarily, people feel threatened when presented with a conflicting situation resulting in a greater tendency towards competition rather than cooperation. This is due to their belief that they would “lose out” so to speak or be subjected to a far lower status resulting in them being relegated to the “losing end” of the spectrum (McCreight 2009, 5). This is despite the fact that Schollmeyer (2005) states that in such a scenario both parties have implemented effective methods of communication between each other.
This theoretical perspective helps to explain why despite the presence of clear lines of communication, cooperation between different departments and agencies is difficult since the parties involved feel “threatened” resulting in a greater tendency towards competition rather than cooperation (Schollmeyer 2005, 8). Such a situation was noted by Dohrn (2003) in his examination of counter-terrorist cooperative agreements between different state and local law enforcement departments wherein the fragmented nature of the system of cooperation coupled with overlapping responsibilities resulted in different departments and agencies feeling that the other was “impinging on their territory” so to speak which made them more competitive rather than cooperative (Dohrn 2003, 130). This resulted in a greater tendency to withhold information as well as perform unilateral operations without other agencies or departments being aware of such actions.
When going over the Deutsch and Coleman theory of cooperation and competition and comparing it to the current situation involving the DHS and other departments and agencies involved in counter-terrorist operations, it becomes clear that this theory helps to explain the current issues surrounding the lack of coordination, reluctance to share intelligence information and fragmentation as opposed to integration Dohrn 2003, 131). Simply put, the mindset surrounding these different agencies and departments is oriented more towards competition rather than cooperation with the challenge involving the future of Homeland Security being the necessity of shifting such a mindset away from competition and towards cooperation Dohrn 2003, 131).
Further examination of the theory of cooperation and competition and potential use towards resolving the current issues surrounding the current challenges surrounding the Homeland Security will be tackled in the findings and analysis section of this research paper where it will be utilized in conjunction with other data to create a clear picture of what strategies can be implemented in order to resolve the identified issues (Waugh 2003, 374). The next section focuses primarily on the dissemination of duties between different departments and agencies. It focuses on the concept of inter-department and inter-agency leadership roles and difficulties involved in implementing such an endeavor.
Leadership and Dissemination of Duties
Leadership is a necessary factor when it comes to combining the different departments and agencies associated with homeland security; however, one of the challenges associated with such an endeavor is the concept known as “acknowledgement of authority”. Caruson (2004) stated that one of the issues when it comes to cooperation across different departments and agencies is that each of them already has a set hierarchy and organizational culture. This creates issues when it comes to cooperation across different departments due to the fact that while it is acknowledged that leadership is necessary for all departments to stick to a specific strategy, the departments and agencies in question are unwilling to give up their individual autonomy and have themselves beholden to an outside party (Caruson 2004, 6).
This results in the issue of fragmentation as opposed to integration that was mentioned earlier on in this research paper which has its roots in the lack of an appropriate leadership structure for the different departments and agencies involved in law enforcement and counter-terrorist activities (Caruson 2004, 8). While it is true that the mandate of the DHS is to protect the territory of the U.S., the fact remains that this does not give it a blank check to basically order around other departments or agencies nor does this necessarily give it a unilateral leadership role when it comes to dealing with identified terrorist threats (White 2010, 49). Despite the DHS being the third largest department in the country, it lacks the specialization and personnel to address the broad spectrum of possible terrorist threats as seen in the potential cases of domestic terrorism brought about by individuals recruited within the U.S. via the medium of the internet (Ramirez 2014, 57). Further examination of the concept of leadership and its application to resolve the current identified issues will be examined in the findings and analysis section.
Public Opinion and the Pursuit of Operations
In response to the September 11 attacks, the Bush administration created the Patriot Act as a means of improving the quality of counterterrorist investigations (Hessman 2003, 9). Its mandate focused on enabling law enforcement officials to have greater powers in relation to investigating and observing potential terrorists within the U.S. At its inception, the law seemed to have a valid purpose and had widespread public support given the events that resulted in its creation; however, over the last few years its utilization has created a considerable number of controversies which can be traced to its abuse by law enforcement agencies (Dawson 2002, 22). One of these is that the term “international and domestic terrorism” under section 213 and 215 of the Patriot Act enabled the police to search an individual’s premises and to observe their phone and internet records for the purpose of protection against the likelihood of terrorist acts without such an individual knowing such acts have been done (Schimmel 2012, 341).
Due to its expediency, it became a common place method for a law enforcement agency to justify a search and seizure operation against a potential suspect under the guise of a domestic terrorism issue when in reality such a case actually fell under the jurisdiction of a normal criminal case. This shows that from its original inception as a means of expediting the process of counter-terrorist operations against potential terrorists within the borders of the country, the Patriot Act became a means for local law enforcement to merely expedite the process of criminal investigation. Evidence of this was noted by Ortiz, Hendricks, and Sugie (2007) where the terminology that law enforcement authorities utilized when describing criminals shifted to towards the use of: “domestic threat”, “national security threat” and “threat to public safety” and other similar phrases. This was done in order to enable the implementation of the Patriot Act when it came to investigative procedures since by labeling such a person as a “national security threat” this in effect “elevated” them into a person of interest that threatened the security of the U.S. despite the fact that such an individual was merely connected to organized crime and drug dealing than they were a terrorist (Ortiz, Hendricks, and Sugie 2007, 93).
Further evidence of the apparent abuse of the Patriot Act, especially sections 213 and 215, was that the use of such terminology to describe criminals was not in use prior to the acts inception and was only widely utilized after it was put in place and referred to a broad category of individuals that often had no links to terrorist organizations (Ortiz, Hendricks, and Sugie 2007, 96). What this section has shown so far is that law enforcement agencies have in effect gone beyond the initial mandate set by the Patriot Act in order to carry out their own operations under the guise of domestic terrorism prevention when in reality a vast majority of the cases was related to ordinary crime prevention. This shows a considerable lack of accountability and coordination between different departments to define the mandate of what is and what should not be labeled as counter-terrorist operations (Donahue Jr., Cunnion, Balaban, and Sochats 2010, 12).
The mere fact that local law enforcement agencies can enact the provisions of the Patriot Act in order to deal with ordinary criminals instead of terrorists showcases a considerable error when it comes to sufficient oversight when it comes to the use of powers that should be limited primarily to counter-terrorist operations (Ortiz, Hendricks, and Sugie 2007, 98). It is due to such a situation that public opinion has been slowly going against the Patriot Act as a whole since its apparent abuse by law enforcement agencies has cast a considerable amount of doubt as to the capacity of the government to implement methods of proper accountability towards the use of such a law (Ortiz, Hendricks, and Sugie 2007, 101). The challenge for homeland security in this case is to mitigate the current negative public perception towards the information gathering provisions in the Patriot act (specifically sections 213 and 215) along with limiting abuses towards its unilateral use by law enforcement agencies as a more expedient method of performing investigations (Ortiz, Hendricks, and Sugie 2007, 109). The inherent problem though when it comes to limiting the actions of other law enforcement agencies is that they are not subject to the direct control of the DHS and, as noted earlier in this research paper, are more inclined towards unilateral action rather than joint ventures.
Not only that, since the DHS does not have direct authority over them, there is no way in which sufficient oversight towards the prevention of the Patriot Act as a means of investigating ordinary crime by law enforcement agencies can be brought about, at least not without significant judicial support (Filiol 2013, 63). This reveals a considerable problem when it comes to preventing negative public perception directed towards the information gathering capabilities that the Patriot Act grants. If sufficient negative public perception is directed towards it, amendments may be put in place to curtail the “powers” of the Patriot Act which would make it more difficult to prevent domestic terrorism (Greener 2013, 30). It is due to this that the actions of law enforcement agencies that utilize the act to tackle local crime must be limited. Methods to resolve such a problem and the recommendations developed by this study to do so will be examined in the findings and analysis section of this paper.
Most of the post-attack responses made it common knowledge that the security efforts of the U.S. suffered poor coordination. This aspect led to the formation of the DHS to foster coordination among all security entities with a mission of preventing future attacks together with enhancing preparedness and response (Kamien 2006, 31). In a bid to mitigate the foreseen challenges facing the DHS and the American fraternity as a whole, this section has so far addressed various issues that are seen as weak links that destabilize the homeland security framework (Barnett and Gaffney Jr. 2005, 18). This can be seen in the example given regarding the competitive nature underlying budget allocation that acts as a barrier towards fostering cooperation. What this section has showed is that the main challenges facing the DHS is poor coordination, cooperation and information sharing across different national agencies and this aspect brings forth the possibility that terrorist attacks will continue to happen if such issues are not mitigated in the future.
Issues with Cooperation and Communication with Other Countries
While this research paper has so far utilized the framework of the theory of competition and cooperation in order to examine the problems with cooperation and communication among the different departments and agencies within the U.S. when it comes to counter-terrorist operations, this section will deal with issues experienced with external agencies (i.e. departments and agencies belonging to other countries). This section focuses on the fact that while it is in the best interest for the different parties involved to cooperate in order to prevent terrorist activities from occurring, there are often cases where information is not shared properly and cooperation between two agencies from different countries is mired in red tape (Friedrich 2005, 33).
This prevents them from creating a more integrated means of information gathering and action resulting in terrorists being able to operate in locations that they otherwise should not be operating in at all. Evidence of this can be seen in the cases detailed by May and Jones (2008) who showed that individuals with terrorist connections were seen in the UK, Qatar, Saudi Arabia and even Indonesia and were utilizing social media in order to recruit more individuals towards the cause of radical Islam. While these cases were previously identified by the U.S. government and the individual departments in these countries were warned about the potential threats, direct action was slow and often resulted in these terror suspects “escaping the net” so to speak or even in some cases having no action done whatsoever (May and Jones 2008, 517). This showcases an issue when it comes to cooperation across different counter-terrorist departments in other countries; however, the presence of such an issue can be considered as being rather unusual since it is in the best interest for the different countries involved to resolve potential terrorist actions from manifesting in the first place and causing more destructive behavior (May and Jones 2008, 518). It is based on this that this section will examine the basis behind the identified issue and determine what methods could be implemented to resolve it in the interest of creating a better global effort towards preventing terrorism.
Perception and America as the “Global Police” of the Planet
The U.S. has been at the forefront of the fight against global terrorist threats and has invested billions into intelligence gathering operations as well as military campaigns in order to halt the spread of terrorist activities (Mumpower, Shi, Stoutenborough and Vedlitz 2013, 1802). While one aspect behind this attitude comes from the September 11 attacks, the fact remains that America’s intervention into the affairs of other countries has a significant precedent (Davis and Albert 2011, 252). This can be seen in the Gulf War, the war in Vietnam, and its actions involving Taiwan and Israel as well as its support for the spread of democracy which it has done through significant investments via foreign aid programs. From these examples alone it can be seen that America has a history of intervention in a wide variety of different international situations which Kapucu (2008) stated is fueled by American ideology involving the concept of manifest destiny and the country’s desire to spread the tenets of democracy. Such an attitude, Kapucu (2008) explained, has created the connotation of the U.S. as being the “global police” of the planet due its economic and military might, its desire to spread its influence throughout the various countries in the world and its actions that intervene in the affairs and actions of many countries around the world.
Such an attitude has fostered numerous positive relationships as seen in the extensive cooperative agreements between the U.S., Japan, Taiwan and numerous other nations (Kapucu 2008, 3). However, on the other end of the spectrum, America’s actions have also sparked a considerable level of enmity from other foreign countries such as China, Russia, and numerous countries in the Middle East (Sigfrinius 2005, 14). Each of the aforementioned countries, and many others like them, have been attempting to create their own spheres of influence in their respective regions yet often encounter the U.S. and its own attempts at gaining more international influence (Bolkcom and Nuñez-Neto 2008, 4). The end result has been the creation of a more competitive rather than cooperative international environment. Evidence of this can be seen in the case of China and the U.S. with China expressing its disapproval over the actions and influence of the U.S. in South East Asia (Jones and Glisson 2009, 38).
There is also the case of the U.S. and its antagonistic relationship with Russia as well as the negative perception that numerous Arab nations in the Middle East have developed regarding the U.S. due to its interference in the Arab-Israeli war which enabled Israel to survive as a country (Khalid and Kamal 2015, 16). This shows that America’s interventionist attitude as well as its actions of attempting to spread its influence has resulted in more countries viewing the U.S. in a negative light. This has further been hampered by the unilateral actions of the U.S. during its invasion of Afghanistan and Iraq which caused more problems than it actually solved (i.e. the creation of terrorist factions) (Moss, Schellhamer, and Berman 2009, 6). It is due to this that America’s role as being the “leader” in the global fight against terrorism is viewed with apprehension by numerous countries who dislike further interference by the U.S. both in their internal affairs as well as in their external actions (Khalid and Kamal 2015, 17).
With this sort of perception regarding the U.S., it is not surprising that this has created issues when it comes to the establishment of proper lines of communication and collaboration involving counter-terrorist activities. Numerous countries simply do not want the U.S. to gain more of a foothold than it already has when it comes to its actions in the global arena. As such, information involving terrorist activities within a country is normally vetted and edited by high-ups within the government before it is passed on (Khalid and Kamal 2015, 18). The amount of time elapsed between a possible suspect has been identified and when the U.S. has information on this individual creates a considerable gap in response time which may lead to such an individual being able to successfully pull-off a bombing or other similar activities before they are stopped. Aside from this, there is also the potential for information to not be passed on at all (Persell and Speraw 2008, 18). Such an act manifests due to the desire of the country to respond to terrorist threats in its own way and not have the U.S. interfere in its domestic issues (Khalid and Kamal 2015, 19).
It is the combination of both the political red tape involved in international cooperation and the fact that some countries may simply be unwilling to cooperate that Johnson (2010) stated causes the U.S. to turn towards the use of unilateral surveillance methods (i.e. spying on terrorists without the permission of other countries) in order to properly track global terrorist operations. Unfortunately, such actions are viewed negatively by numerous countries as a violation of their domestic security which creates even more issues and a greater reluctance to cooperate (Johnson 2010, 1329). From the point of view of the theory of cooperation and competition, the mistrust inherent from all the parties involved prevents cooperative actions from being brought about. In the situation that was just described, the U.S. knows that there are countries that are simply not willing to cooperate when it comes to counter-terrorism operations which it views as being detrimental towards preventing the spread of terrorism and, a result, a considerable level of resentment develops (Johnson 2010, 1330). The U.S. would view such countries as merely being “free riders” to the current global operation towards preventing the spread of terrorism (i.e. overtly supporting the action but internally hampering it due to a lack of cooperation) which causes the U.S. to rely more on its own unilateral actions (Johnson 2010, 1330).
On the other end of the spectrum, the aforementioned countries are wary of the intentions of the U.S. and the long term consequences of America’s role in the “fight against terror” which results in their uncooperative behavior. Both of these behaviors from the U.S. and the countries are manifestations of the theory of realism in international relations which ascribes to the notion that states are unitary actors that will always pursue paths of self-interest (Johnson 2010, 1331). In this case, the countries that have just been mentioned are wary of the path of self-interest that the U.S. is pursuing since it may impact their domestic and international agendas which they are also pursuing due to their own self-interest (May, Sapotichne, and Workman 2009, 173). The end result is that this creates a more chaotic system for cooperation (which is also explained in the theory of realism) resulting in a greater likelihood for the different countries involved in counter-terrorism operations to restrict information sharing and focus on their own activities rather than cooperate with one another.
From a homeland security perspective, this level of uncooperative behavior between different countries hampers the ability of the U.S. to properly respond to external terrorist threats. As evidenced by the case mentioned in the initial section of this literature review, potential threats that can impact the U.S. can come from multiple countries due to how recruitment through the internet can create domestic terrorists (Busch and Givens 2012, 4). However, with the current state of cooperation which is mired in mistrust, it has become difficult to foster significant methods of joint action such as information sharing and bi-lateral operations to detain potential terrorists across multiple countries (Pantucci 2007, 3).
Sovereignty and U.S. Interference
Joint international operations to prevent the spread of terrorism is a necessary aspect of present day counter-terrorist operations; however, one of the issues when it comes to its implementation is the viewpoint of countries involving the fine line between cooperation and interference with a nation’s sovereignty (Schneider 2013, 17). As noted in the previous section, numerous countries have issues when it comes to the actions of the U.S. as a type of “global police” when it comes to its actions involving terrorism and international conflicts. With this in mind, China, Russia, Saudi Arabia and other countries around the world are adamant in not allowing the U.S. to have any form of influence over its domestic policy agendas regardless of the potential impact that terrorist threats may have on them (Zimmerman 2011, 153). The end result is that joint counter-terrorism operations become infeasible since these countries simply do not want to cooperate when it comes to allowing the U.S. to “take the lead” so to speak when it comes to addressing the problem of terrorist activities within their borders (Johnson 2010, 1328). This has extended to not responding to requests or warnings from the U.S. when it comes to identified terrorists being in their country or even requests for intervention in order to capture these suspects. Simply put, these countries desire a “hands off” policy from the U.S. resulting in terrorist suspects continuing their operations unabated (Dodsworth 2012, 628).
From the Deutsch and Coleman theory of cooperation and competition this attitude is described as a direct result of a distinct lack of trust on the behalf of these countries resulting in a adversarial rather than cooperative behavior. Not only that, studies such as those by Hill, Oliver, and Marion (2010) explained that countries such as Russia, China and those in the Middle East who are attempting to create their own power base by virtue of their greater economic and military might in their respective regions are less likely to cooperate with the U.S. when it comes to counter-terrorist operations as compared to countries such as the Philippines (Maurer and Johnson Jr. 2013, 5). The reason behind this is the fact that countries such as the Philippines do not have the economic nor military capacity to create what is known as a “sphere of influence” and, as such, are more amenable towards diplomacy and reliance on a much powerful country for their security needs (Hill, Oliver, and Marion 2010, 897). Evidence of this can be seen in the joint military exercises between the Philippines and the U.S. as well as the fact that U.S. has far more influence and access to the Philippines as compared to China, Russia and Saudi Arabia (Hill, Oliver, and Marion 2010, 898). Overall, this creates a considerable homeland security challenge for the U.S. since various countries where radical terrorist elements are known to exist are uncooperative and reticent towards their involvement within their country’s borders. This allows potential recruitment drives to continue unabated and further increases the likelihood of more terrorist attacks (Hammond 2008, 219). It is with this issue in mind that the next section of this research paper focuses on the use of soft power to potentially address the issue of uncooperative behavior from other countries when it comes to counter-terrorism operations.
Utilizing Soft Power to Address Issues on International Counter-Terrorism Cooperation
In a bid to address the underlying mission of the homeland security, it is good to understand that the burgeoning campaign against terrorism is a multifaceted endeavor. The federal machinery has to deploy every tool at its disposal to wage this fight; for instance, international training, law enforcement, finance, diplomacy, as well as the new tools that are being invented. In this regard, it is noteworthy to review the works of Joseph Nye, viz. Soft Power: The Means to Success in World Politics. Soft power is a concept developed as an alternative to use of force, coercion, or monetary compensation to persuade others to adhere to what one wants (Nye 2004, 74). Nye (2004) had keenly observed how the American society was struggling with hard power, yet enemies were in a position to not only hit, but also hit hard regardless of the alleged preparedness of the US security agencies. Nye’s conviction of power as possessing the ability to lure others to get to the preferred destination is currently given a chance albeit in part by various security entities across the world (Nye 2004, 98). The US Congress has shown reluctance in allocating more money to cater for security matters. In the last decade, in spite of the security concerns, the budget allocation to ensure a more secure homeland has always fallen short. Consequently, planning and implementation have overlooked key security factors that gradually continue to affect the homeland security negatively. The US government can adopt soft power and save chunks of taxpayer’s money used on hard power like the military. Soft power and hard power should be used alongside each other, but the former should be granted much attention in terms of implementation and financing.
It is evident that soft power is hugely overlooked, and this aspect contributes partly to the current fall in the US power influence over the past five decades. The old image of the US as the representative of democracy and a symbol for others to emulate has declined dramatically. The use of hard power by the US has doubled the fear rather than instilling optimism. The US security entities have developed an old versioned tendency of using tactics employed in past wars to address current concerns. While there are positives to be drawn from history, facing the 21st Century terrorism requires a paradigm shift. Since the case is new, security agents should adapt quickly to new measures and act in new ways. So far, the existing partnerships encouraged by President Obama’s administration are yet to materialize, as there is still overlapping of critical roles by different intelligence partners. The CIA’s chronic failure prior to the September 11 attacks to inform partner agencies about the names of the alleged terrorists in the country enabled them to stay and orchestrate the attacks. Therefore, information- sharing continues to suffer from significant flaws. In order to learn from past events, it is necessary to change the bureaucracy that encourages information hoarding and empower experts to take full responsibility for their roles with less closed systems. This hindrance can be overcame by developing a paradigm shift whereby experts have the power to react to an urgent situation at best of their knowledge instead of waiting for commands from the top, which are time wasting and uninformed in most cases (Puyvelde 2013, 142).
Despite the many advantages of soft power, it has some shortcomings. Americans are scientifically oriented, and thus they resist soft power because they find the design behind it difficult to trace and research. As a society, the US is used to quick answers and it seeks immediate satisfaction. Unfortunately, soft power is a long diplomatic investment with no assured outcomes. This aspect explains why the US government prefers hard power even though it is expensive. In addition, soft power is not purely owned by the government like the case with hard power. Many public and private entities engage in soft power, thus making it hard to collect information together. After evaluating the social learning theory, one is in a position to identify that not all cultures are receptive of other nations’ strategies and ideas (Lieven and Hulsman 2006, 61). In this regard, these theorists challenge soft power as not many cultures find the US values and ideologies admirable to follow. Therefore, there is a possibility that soft power can backfire especially when in control of the wrong people.
Cultural exchanges have developed to serve as measures to control national security. Through cultural exchanges, different people are in a position to gain better understanding of others. Similarly, other individuals get the opportunity to acquire greater understanding of the US mainstream culture. For instance, some scholars attribute the fall of the Soviet Union to social exchanges gained after visiting the US the international relations theory advocates for multilateral relations between the state and non-state actors. Developing mutual understandings is one way through which the DHS can achieve its mission of ensuring security at both domestic and international levels. This theory further suggests that mutual relations are difficult since every state has its own ambitions and if they fail to reciprocate with those of the other state, then cooperation is not possible.
Problems with the DHS
The current workforce in the DHS is inadequately equipped in terms of resources, empowerment, and training. For example, after the September 19 2014 White House incident in which a man managed to jump over the White House fence, Cummiskey, a former DHS agent, argued that the security flaw was purely attributable to the lack of funds (Shear and Schmidt 2014). Further investigations backed this claim by showing that several agents on duty had no appropriate skills to handle the situation. In addition, the majority had no idea on how White House Communication radio operated under such circumstances. This assertion holds due to the lack of enough financial resources, which should not be a reason to expose prominent leaders such as the president to any sort of security threats.
Despite the evident commitment and progress demonstrated amongst government agencies, this review notes that there has been lacking professional exchange of intelligence information amongst security agencies. Furthermore, military and law enforcement training is yet to upgrade to the standards of the 21st Century technology that can assist in promoting the US security level (Rychnovska 2014, 27). It is about 14 years down the line since the September 11 attacks, but the US government continues to delve into research and forums to develop strategies to enhance the homeland security. It has become increasingly evident that the U.S. security entities are suffering due to the lack of interconnectedness. In light of this impasse, President Obama, in a directive to evaluate the DHS and its efforts towards counterterrorism, retaliated that the DHS is inseparable from other security agents and they should be functionally thought as a unit rather than separate entities (LaPira 2014, 230). Contrary, the federal state still faces conceptual and functional differences. This aspect has weakened integration, efficiency, and cohesive approaches that promote the national security since the bureaucratic system inhibits the formulation of ways that reflect this reality.
So far, the Government Accountability Office’s (GAO) appraisal of the federal government and its security agencies indicates that there has been positive progress yet not enough to guarantee sustainability. For example, in a report done on September 2013, GAO reported on the activities that DHS had taken in regard to the use of resources outside the US. The GAO established that the DHS had not identified strategic plans like target zones to combat crime and secure the US borders. The DHS also lacked mechanisms to capture resource deployment neither did it have a reliable cost data to make informed resource-allocation decisions. This aspect implies that the DHS is failing significantly in planning since it does not consider data monitoring and analysis on expenditure abroad. Without this data, it is hard to disseminate funds on future programs. In addition, this aspect manifests poor intelligence planning and data collection gaps, hence poor analysis. In a bid to avoid this issue, the DHS must inform its resource deployment outside the US as well as encourage screening.
Theoretical Framework to be utilized in the Analysis
In this research paper, the theoretical framework that will be utilized is the Deutsch and Coleman theory of cooperation and competition which operates under the premise that relationships between differing organizations that are attempting to achieve the same goal are subject to a mix of competitive and cooperative motives. This manifests in the following instances:
Negative Interdependence
Under this element, the success of one party correlates into the failure of the other. Within the context of organizations pursuing the same objective, in order for one to achieve success, the other must fail. This type of relationship was noted by Barry (2009) as manifesting in the numerous instances between law enforcement agencies within the U.S. wherein budgetary allotments to each agency or department was dependent on their inherent success. From an organizational management perspective, such a system encourages agencies to pursue success in order to increase the amount of funding they receive resulting in supposedly increased performance (Barry 2009, 28). The inherent problem with such a system is that it encourages inter-agency and inter-department competition for funding and helps to explain why information regarding potential terrorism activities is being withheld or why different departments and agencies pursue counter-terrorism operations unilaterally instead of cooperating with each other. Under the negative interdependence perspective of the theory of competition and cooperation, the differing law enforcement agencies simply view the failure of the other agencies as something that contributes towards their own success since it results in increased funding (Bajorek 2005, 875).
Positive Interdependence
Positive interdependence on the other end of the spectrum correlates the success of one department or agency with the success of the other or even the failure of one department or agency with the failure of the other. Under this theoretical perspective, it is assumed that the combined goal that the agencies or departments are trying to achieve, in this case safeguarding U.S. territories from terrorist action, is more important than their individual mandates. Kiltz and Ramsay (2012) clarified this by explaining that while negative interdependence is a manifestation of competition between different organizations, positive interdependence is a manifestation of cooperation. In this case, agencies and departments seek to cooperate with each other towards a perceived shared goal regardless of the different organizational cultures or mandates that each is subject to (Kiltz and Ramsay 2012, 5). Examples of this can be seen in the case of multi-lateral trade relations between different countries that have manifested as a direct result of globalization and the interconnected economies that have come about because of it (Kiltz and Ramsay 2012, 7).
Countries that are part of the current system of international trade and commerce have a shared interest towards preserving the continued flow of products and services and, as such, they follow rules, guidelines as well as cooperate with one another in order to ensure that products and services from different companies and countries continue to span the globe (Kiltz and Ramsay 2012, 9). It is this common interest towards a shared goal that eschews normal competition in light of the need to ensure that global trade continues unimpeded. Another example that is more relevant to the current focus of this research paper is the levels of cooperation and information sharing seen between different countries that take part in the global fight against Islamic terrorist organizations (Kiltz and Ramsay 2012, 10). Countries such as the U.S., the UK, the Philippines, and even France share vital information and even commit resources in order to combat terrorism. What this shows is that cooperation is possible under a shared common interest and showcases the possibility that despite the current issues impacting cooperation and information sharing among the different agencies and departments that take part in preventing terrorist operations, these organizations may be able to create a better cooperative relationship in the future. It is this possibility that will be examined in the findings and analysis section of the study.
Approach
There are existing gaps in literature in regards to the state of national intelligence service in the United States. A critical review of literature reveals that both classical and contemporary studies concentrate mostly in socio-political theories without keenly revising intelligence and security aspects. For the past few decades, it is evident that the interests of the US foreign policy have captured major headlines at the expense of addressing national security intelligence. In fact, before the formation of DHS, there was minimal redress given to national intelligence. This study will assist in filling the eminent gaps in literature by applying a number of models, theory and frameworks. Behavior change in the management of security affairs is perhaps required in order to reverse the current trends.
Since this research study will be exploratory, theoretical frameworks will be fundamental. An exploratory study of this nature will assist in eliminating or deterring any preconceived notions about national security intelligence. Although there is some amount of knowledge that is freely available in public, this research study will be keen to avoid in assumptions. Hence, the validity of the findings and conclusions made in the research paper will be tested using valid theories.
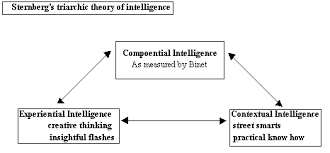
Examining the challenges faced by DHS will only be testable using theoretical frameworks. Generalizations, interpretations, research designs and hypotheses will be employed in this study. In addition, the theoretical framework used must be supported or substantiated by past research studies. Descriptive theories that will be used in the study will be tested for validity using descriptive research studies. Besides, this study will employ correlation research. The latter will be tested using explanatory theories (Friedman 2011, 84). This study will specifically use the Sternberg’s intelligence theory in order to point out individuals or state organs that must act proactively to improve intelligence system in the United States.
The hypothesis to be tested
Poor gathering and utilization of intelligence data will continue to impede the performance of DHS in the future.
Research Design/Methodology
Introduction
The issue of insecurity has been a sensitive subject to the US government since the September 11 attacks. In this regard, preventing such detrimental occurrences is vital for the harmonious coexistence of the different individuals in the country and global peace in general. Therefore, investigating the underlying issues that trigger acts of terrorism and general insecurity is significant for the management of security and fostering international peace. Additionally, analyzing various mechanisms of the security systems is essential for the development of conclusions that facilitate the understanding of the efforts put by the intelligence agencies such as the Department of Homeland Security (DHS) in dealing security threats (Richelson 2010, 124). For this reason, developing a body of knowledge is necessary through conducting extensive research on the security issues affecting the US government. This paper will provide a description of how research on security matters affecting the US can be conducted to derive meaningful conclusions.
The research approach
Selecting an appropriate research method is essential for conducting an adequate research on security matters. This assertion holds because the nature of security issues takes a multidimensional perspective, thus resulting in the need for the analysis of the social, economic, and political aspects of the problem (Patton 2010, 215). In this sense, research design that covers the different dimensions of the US security issues is necessary for the investigation to be meaningful to the parties involved. Therefore, employing qualitative research methods is appropriate for such a research problem.
A qualitative research method is an inquiry that analyzes data derived from verbal and behavioral expressions in natural settings (Silverman 2001, 82). Qualitative research enhances the capture of vital information regarding beliefs, feelings, values, and motivations behind certain behaviors that cannot be easily obtained through quantitative methods (Marshall and Rossman 2010, 120). In this respect, the application of qualitative approaches to inquiry in security matters would consider the beliefs, values, feelings, and motivations behind acts of terrorism. Adopting a qualitative approach to investigate the US security issues ensures that the public is in a position to share what is important regarding its security concerns. To the researcher, the adoption of qualitative methods implies that the identification of critical variables like religious beliefs, economic conditions, and political leadership is enhanced due to the better understanding of the research problem before its execution (Saller and Mutlu 2012, 210).
Various qualitative approaches are applicable to the security research problem including historical analysis, ethnographic research, phenomenology, ethical inquiry, and case studies. For instance, the ethnographic approach can be used in the research project to investigate a community associated with terrorism by identifying the goals of the inquiry then selecting a site before the establishment of rapport. Observations can then be made whereby field notes are written as data is collected (Packer 2011, 278). However, due to the ineffectiveness of ethnographic and observational techniques in security studies, the LAMP approach would be effective for this case.
Reasons for applying qualitative methods in the research project
Applying qualitative approaches in the investigation of the US security issues, which have been constantly under the management of agencies such as the DHS, is beneficial in several ways. Qualitative methods of research provide an in-depth analysis of the insecurity phenomena that has affected the US and the international community. In this respect, the researcher would be in a position to utilize analytic strategies to get an extensive understanding of the insecurity research problem (Honig 2007, 710).
Practical and invaluable information on security issues can be obtained through qualitative methods of research. This goal can be attained through the application of predictive techniques that enhance the foresight of insecurity events such as the September 11 terrorist attacks. The intentions of the actors and their attitudes towards the detrimental effects of such attacks could be considered to gauge the extent of the implications. Similarly, suspects of terrorism could be investigated and their behavior evaluated to attain invaluable practical information on their beliefs, values, and motivation behind the heinous attacks (Clauser and Goldman 2008, 178).
Qualitative research methods are necessary for the identification of the structures existing in various agencies that have a bearing on security issues. Engaging agencies such as the DHS in focus group discussions and interviews would unmask the underlying matters that portray the interdependencies and values that the organization considers as necessary for the enhancement of security in the US. Similarly, engaging in an in-depth analysis of the perceptions and objectives of the major actors would provide dependable data that indicates the interdependence of various structures that facilitate the execution of acts of terrorism (Dolnik 2013, 120).
The application of qualitative methods of inquiry in intelligence issues enhances flexibility. Qualitative approaches ensure that the limitations that exist in security variables are dealt with in a bid to obtain meaningful data (Schmid 2013, 633). In this respect, the analyst can specify the courses of action and frame the possible scenarios to predict the potential security events in a particular society. Therefore, determining the potential alternate events could enhance the predictive nature of the study on the underlying issues about security in the US.
Special Considerations
Conducting inquiries on security and intelligence problems requires special considerations for the attainment of a successful research process. Factors like the study base, research timeline, ethical issues, and reliability, and validity need to be considered for the research to be efficient. The study base represents the cohort group that the research will be focusing on (Shepherd 2012, 139). In this case, the source population would be the individuals under the management of the DHS agency, individuals believed to possess reliable information about terrorism activities, humanitarian organizations, victims of the September 11 attacks, and any other relevant parties. In this regard, the study group for the proposed research project is broad in nature since the effects of the problem transcend the American society.
The research timeline employed in the qualitative approaches should be considered. This aspect implies that the qualitative data collection tools need to be framed within a particular span of time that covers the problem extensively (Patton 2014, 523). In a bid to understand the background of intelligence and security matters leading to the September 11 attacks, the qualitative methods would employ a historical approach before applying other methods such as interviews in the research process.
Ethical issues would be a matter of special consideration for the research project. An ethical inquiry would be conducted to comprehend ethical issues that surround the US security. Additionally, the research process would consider ethical issues, which are necessary for conducting a morally acceptable qualitative research. This aspect would entail the power relations existing between the researcher and the respondents, privacy and confidentiality, consent, anonymity, and confidentiality (Josselson 2013, 107). In so doing, the research would be in line with the ethical standards, which are critical for researchers in their qualitative research undertakings regarding the intelligence and security aspects of the American society.
Limitations of the Research Approach
The qualitative approaches would be employed in the study including the use of predictive analysis that employs the Lockwood Analytical Method for Prediction (LAMP) process. Unlike other research methodologies, the LAMP approach is not limited in its approach due to its sophisticated nature and strong affiliation to the intelligence community. The approach mitigates the challenge with alternate future concerning exponential explosions. The approach prevents room for ambiguity in its procedures, thus enhancing certainty. However, the approach cannot quantify the probability of a future occurrence as it can only provide the prediction of the most likely future events.
Measurement of variables
The nature of the study that would be conducted entails the analysis of the cause, effect, and intervening variables. The research would identify the effects of insecurity in the US and then identify the cause before establishing the relationship between the two aspects that make up the dependent and independent variables respectively. In this case, the intervening variables would define the link between the cause and effect variables. Therefore, measuring the dependent, independent, and intervening variables would be essential for the facilitation of objectivity, reliability, and validity of the research findings. The measurement of variables like individual behavior, attitudes, and security policies would employ the use of measurement scales such as nominal, ordinal, interval, and ratio scales (Saller and Mutlu 2012, 178).
Collection and assessment of data
The data collection and analysis phase in the study is vital for obtaining valid and reliable results that would be used to make conclusions pertaining the intelligence issue in the US. Since the traditional methods of predicting future events concerning intelligence have experienced shortcomings, the use of the LAMP method would be appropriate in this case. The LAMP approach is an innovative method that was created by Dr. Jonathan Lockwood in the 1990s. The methodology is vital in this regard since it incorporates sophisticated planning and analytical procedures that consider empirical data in determining future events in the Intelligence sector (Lockwood 2013, 27).
In the case of this study, the LAMP approach would enhance the forecasting of possible threats that would be faced by the US Intelligence departments in a bid to work towards the curtailment of the problem. Issues like possible terrorist attacks by extremists like the Al Qaeda, cyber-attacks, and nuclear weapons issues would be managed through the collection and analysis of empirical data on security aspects. In this study, the assessment and prediction of future intelligence would not focus on probabilities, but on presumptions that trigger future events. Therefore, the LAMP approach presumes that various parties act based on their rationality. In this sense, the consideration of qualitative techniques in the assessment of human behavior regarding security matters is essential. Additionally, it would be indispensable to understand that the actors have the freedom to choose what is best for their country considering its safety and move towards prosperity. The following twelve steps involved in the LAMP process would be effective in facilitating security and Intelligence issues affecting the US.
The first step in the analysis of the qualitative data would be the determination of the predictive issue. Defining the issue is a vital step in the LAMP methodology since it facilitates the consideration of various actors, their courses of action, and implications for the future. Specifying the national actors involved in the US intelligence system would be the next step in the application of the LAMP methodology. In this phase, the researcher determines the national actors that have a bearing on the problem. In this regard, the US and the terrorists’ state agencies would be considered. Limiting the scope is essential in this step, and thus five actors are sufficient. Carrying out a thorough study of the perceptions of the national actors and their intentions constitutes the third step in the LAMP process. The analyst endeavors in historical research at this step to determine the implications of the past for the current and the future (Prunckun 2014, 67).
The fourth step in the LAMP approach is the specification of the possible courses of action for the various actors in the intelligence fraternity. This move enhances the prediction of forthcoming events on security issues concerning the US intelligence case (Beebe and Pherson 2014, 122). The fifth step involves the determination of the scenarios that surround the comparison of the alternate futures. This aspect would facilitate the analysis since it focuses on the determination of assumptions that trigger the activities of the national actors involved (Lockwood 2013, 56).
The sixth step would be calculating the number of alternate futures with respect to the scenarios. The formula for the calculation is “XY=Z whereby X is the number of courses of action, Y is the number of actors, and Z represents the comparable number of alternate futures” (Lockwood 2013, 58). The seventh step in the LAMP approach is the comparison of alternate futures in a pair wise manner. In this phase, two alternate futures are compared to determine their probability. The eighth step entails ranking the alternate futures depending on the number of votes garnered by each scenario from the lowest to the highest. An analysis of the impacts of each alternate future characterizes the ninth step in the LAMP process whereby the analyst postulates the “future history”. Subsequently, the tenth step would entail the determination of the current “focal events”, which are responsible for the occurrence of the alternate future. The last step in the LAMP process entails the development of statements that focus on the potentiality of the transposition of a particular alternate future into another. The possibility of the implications of an alternative future to transpose into another should be considered since it can interfere with the prediction of future security events in the US (Lockwood 2013, 57-65).
Conclusion
Addressing insecurity issues in the US and the international community requires in-depth research to address the issue comprehensively. In this case, the research problem takes the qualitative approach that employs the sophisticated analytical method through the LAMP process. Limitations such as subjectivity issues can be dealt with by applying professional skills that uphold objectivity, which is facilitated by the LAMP procedures that would be used in the research methodology. The measurement of variables in this research would emphasize the aspects of reliability and validity in the prediction of the alternate future. The twelve steps involved in the LAMP process are significant for the effective analysis of the problems encountered by the US intelligence, thus enhancing the predictive nature of the study. Therefore, findings from the study on the US security and international intelligence would result in meaningful conclusions.
Special Considerations
Conducting inquiries on security and intelligence problems requires special considerations for the attainment of a successful research process. Factors like the study base, research timeline, ethical issues, and reliability, and validity need to be considered for the research to be efficient. The study base represents the cohort group that the research will be focusing on (Shepherd 2012, 139). In this case, the source population would be the individuals under the management of the DHS agency, individuals believed to possess reliable information about terrorism activities, humanitarian organizations, victims of the September 11 attacks, and any other relevant parties. In this regard, the study group for the proposed research project is broad in nature since the effects of the problem transcend the American society.
The research timeline employed in the qualitative approaches should be considered. This aspect implies that the qualitative data collection tools need to be framed within a particular span of time that covers the problem extensively (Patton 2014, 523). In a bid to understand the background of intelligence and security matters leading to the September 11 attacks, the qualitative methods would employ a historical approach before applying other methods such as interviews in the research process.
Ethical issues would be a matter of special consideration for the research project. An ethical inquiry would be conducted to comprehend ethical issues that surround the US security. Additionally, the research process would consider ethical issues, which are necessary for conducting a morally acceptable qualitative research. This aspect would entail the power relations existing between the researcher and the respondents, privacy and confidentiality, consent, anonymity, and confidentiality (Josselson 2013, 107). In so doing, the research would be in line with the ethical standards, which are critical for researchers in their qualitative research undertakings regarding the intelligence and security aspects of the American society.
Findings and Analysis
Introduction to Data Analysis
This section of the study will focus on steps four through twelve of the analytical methods outline in the LAMP methodology. Steps one through four have already been tackled in the previous sections in this research paper as noted in the introduction and literature review sections. What will be determined is which of the possible alternate futures when it comes to future challenges to homeland security are more likely to occur. These alternate futures takes into consideration the Deutsch and Coleman theory of cooperation and competition and thus the scenarios involved will focus on either of the two aforementioned factors manifesting when it comes to inter-agency and inter-department cooperation and coordination.
LAMP method step 4: Specify all possible outcomes
This section of the paper will be building up on the views of the theory of competition and cooperation in order to specify the possible outcomes that come about through the interactions of different agencies and departments when it comes to cooperation in counter-terrorism operations.
Identified Challenge
Utilizing the theory of competition and cooperation, it can be seen that the mindset surrounding these different agencies and departments is oriented more towards competition rather than cooperation with the challenge involving the future of Homeland Security being the necessity of shifting such a mindset away from competition and towards cooperation.
Scenario Development
Utilizing the LAMP methodology, several possible scenarios were created based on the theory of competition and cooperation wherein there is either cooperation, competition, both or neither and explain the basis behind each scenario and how likely any one of them is to occur based on what is currently known.
Limitations of the Analysis
This research paper acknowledges the fact that there could potentially be an unlimited number of possible scenarios that could manifest as a direct result of the possible interactions between the parties involved. It is due to this that the examination centers primarily on anti-terrorism activities and not on any further interactions between the different agencies and departments.
Primary Focus of Analysis
The primary focus will be on the interactions between the DHS and agencies such as the FBI, CIA and local law enforcement departments. The secondary focus of the paper will be on the interactions between the DHS and its international counterparts.
Categorization of Interactions
The investigation will categorize the levels of interaction based on the Deutsch and Coleman theory of cooperation and competition resulting in the following categories: 1) Cooperation; 2) Competition; 3) Cooperation and Competition. The definition behind each potential scenario is listed below:
Cooperation
In this scenario, the different agencies involved (both local and international) would realize the folly of their belligerent behavior when it comes to cooperation and information sharing. As such, they would engage in more open dialogues in order to foster better cooperative behavior, information sharing as well as joint operations in order to tackle the problem of terrorist activities. Under this scenario, issues such as who shall lead or problems related to territories and jurisdictions are eschewed in favor of identifying and capturing terrorist suspects in order to prevent further deaths from occurring.
Competition
In this scenario, despite the need for cooperative behavior in order to properly handle terrorist threats, different departments and agencies (both locally and abroad) continue to perform unilateral actions. There is little in the way of significant information sharing, cooperation or even proper interactions between the different agencies. Each party involved performs their own actions based on their own internal decisions without taking into consideration the opinions of other agencies and external parties.
Competition and Cooperation
This scenario is a combination of both competition and cooperation wherein there is some cooperation but the interactions between the two parties is mostly competitive. Information sharing and cooperation is done but only in select circumstances where it is necessary to tackle large identified threats. An example of this type of scenario in action can be in the case of the U.S. and various Middle Eastern countries when it comes to the threat of ISIS and its growing expansion in Iraq and Syria. Cooperation between the different parties is fostered by a clear identified threat yet is still subject to considerable uncooperative behavior when it comes to interference in internal domestic affairs.
LAMP Method Step 5: Major Scenarios that may occur
Hypothetical Scenario # 1 DHS Emphasizes the Possibility of Major Terrorist Attacks Due to Continued Uncooperative Behavior
In this scenario, the DHS would emphasize the possibility of several major terrorist attacks occurring in cities both in the U.S. and abroad resulting in hundreds of deaths due to continued uncooperative behavior. These attacks would have been perpetrated by domestic terrorists who were recruited through the internet resulting in the development of several underground terrorist cells in various countries. The DHS would emphasize that such attacks could be successful due to a lack of communication and collaboration between different agencies and departments (both foreign and local) which enabled radical Islamists to gain a foothold in numerous areas. The main culprits behind these attacks would be unknown since there would have been little in the way of significant collaboration in order to identify threats and bring in suspected terrorists.
Basis of the Hypothetical Scenario
The basis behind the plausibility of this scenario can be traced to studies such as those by Karl (2011) and Nieto-Gómez (2011) who explained that while the different departments and agencies within the U.S. and other countries are individually capable of preventing threats on their own; their capacity to do so is greatly increased through better communication and joint operations. With the current issues plaguing the system, there is a greater likelihood of domestic terror scenarios occurring as a direct result of foreign recruiters in effect converting local citizens into radical jihadists. Thus, by emphasizing the current vulnerabilities, the DHS would seek to create a shared goal to help facilitate information sharing and cooperation.
Hypothetical Scenario # 2 DHS seeks Executive and Congressional Interference
Due to an apparent lack of effectiveness of the DHS and other agencies when it comes to cooperative behavior in preventing terrorist operations within the country, the office of the President along with the U.S. Congress on the urging of the DHS would enact new measures that encourage cooperation and communication between the aforementioned organizations. These measures seek to streamline information sharing and cooperation through the use of better internal systems of communication, joint task forces as well as seminars involving the different organizations involved. It is hoped that through the use of these methods, this would foster better relations between the agencies involved.
Basis of the Hypothetical Scenario
The basis behind this hypothesis was noted in the developments studied by Bjelopera (2015) and George (2010) who stated that Congressional interference in the operation of law enforcement agencies was increasing over the years due to the “power of the purse” (i.e. the capacity to allocate budgets). As a result, operations within numerous law enforcement departments have been placed under more congressional scrutiny leading to the potential for new measures being put in place if the lack of communication and cooperation between the different organizations involved impairs their capability to address the problem of terrorism.
Hypothetical Scenario # 3 Use of Soft Power
In a bid to improve its relations with other countries, the U.S. would actively pursue the use of soft power strategies. This would involve the use of more extensive foreign aid programs, education scholarships as well as increasing the amount of economic support that it would grant to a particular country.
Basis of the Hypothetical Scenario
The basis of this strategy was to change the perception of the country towards the U.S. in such a way that they would become more amenable towards cooperating when it comes to counter-terrorist activities. The end result would be greater access to information regarding potential terrorist threats within that country and better joint operations to target these threats.
Step 6 LAMP method: Analysis of the Total amount of alternate futures iterations that can be found in each possible scenario
In this scenario the total actors consists of the DHS and OAD (Other Agencies and Departments). The basis behind the use of the OAD and DHS distinction is due to the fact that the examination focuses on the actions of the DHS and its cooperation with other agencies as a “leader” in counter-terrorist operations. As such, the other organizations are thought of as singular actors despite being different organizations. It should also be noted that examining the possible individual interactions between the DHS, FBI, CIA and local law enforcement agencies would result in excessive data that would merely be repetitive. The initial table that can be seen after this section showcases the alternate futures that possibly come about (Prunckun 2014, 54). The table is separated into two columns and is then subsequently numerically arrange from 1 to 9 in the initial column that can be seen (Prunckun 2014, 54). The next two columns show the possible courses of action that the DHS and OAD could possibly find themselves in. The table can be seen below with the steps utilized to make the connection also shown:
Ay= Z
A = this character represents the amount of possible actions that is available to each agency/department being analyzed (3)
B = this character represents the number of actors that will take part in the scenarios (2 – OAD is the trigger point and accounted for by the scenarios)
C = this character represents the total amount of the possible alternate futures that can come about from this examination (9)
Scenario #1 (3²= 9) AND
Scenario #2 ((3²= 9)
Scenario #3 ((3²= 9)
Table 1: Alternate Futures.
Step 7 of the LAMP methodology: Comparison of possible alternate futures that may occur between the DHS and OAD via pair wise comparison and Step 8 of the LAMP methodology: Ranking the alternate possible futures between the DHS and OAD based on which is the most likely and least likely to occur.
This research paper will now utilize the seventh step of the LAMP methodology to examine the alternate futures utilizing a pair wise method of comparison. This method of examination operates under the assumption that the alternate futures that are being examined are those which are to occur in that particular situation (Prunckun 2014, 55). For example, the first alternative future DHS (C) VS OAD (C) will be compared to other alternative futures to the extent that only the top two most likely will be the outcome or on the other end of the spectrum the most unlikely to occur (Prunckun 2014, 57). The validity of these choices will be examined afterwards.
The examination consists of the following:
A = this character deals with the total amount of paired futures that will be examined
B = this character deals with all possible iterations of alternate futures that will be examined
A = (b — 1) + (b — 2) etc….. + (b — b)
b = this character details the nine possible alternate futures that will be examined
A = (9-1) + (9-2) ….… + (9-9) = 36 pairs will be examined
Before proceeding, it is necessary to note that this research paper was unable to utilize surveys in order to gain the opinions of various experts in the field so as to create an effective ranking system. As such, the ranking system utilized in this LAMP methodology is based on the researcher’s assumptions utilizing academic research and the theory of cooperation and competition that was utilized as the backbone behind the analysis conducted.
After examining the different alternative futures, the ranking system showed the following alternative futures as being the most likely to occur:
- Alternate Future # 1 Cooperation (C) + Cooperation (C): Rank 1
- Alternate Future # 5 Cooperation and Competition (CCP) + Cooperation and Competition (CCP): Rank 2
- Alternate Future # 2 Cooperation (C) + Competition (CP): Rank 3
- Alternate Future # 7 Cooperation (C) + Cooperation and Competition (CCP): Rank 4
The selection and ranking of these alternative futures is based on the theory of competition and cooperation which explained that the futures selected were the most likely to occur when it comes to developing agreements between different organizations.
The table showed that the least likely alternative future to occur is:
Alternative Future # 4 Competition (CP) + Cooperation (C): Rank 9
This assertion is due to the unlikely manifestation of a scenario where the DHS would be unwilling to cooperate yet the different agencies are pushing for cooperation.
Comparison of the Most Likely Alternative Futures to Occur
The following selection consists of the most likely and least likely alternative futures to occur based on the ranking system utilized. This aspect of the study focuses on how each potential alternative future would impact the hypothetical scenario that was elaborated on in the initial portion of this section. Rank 2 Alternate Future Cooperation and Competition (CCP) + Cooperation and Competition (CCP) will be compared against the other three high ranking alternative futures. The basis behind its use is due to how it incorporates both cooperative and competitive scenarios and thus acts as a sufficient neutral factor for the examination.
The ranked alternative futures will be utilized to examine the hypothetical scenarios based on the likelihood of them occurring. As such, hypothetical scenario # 1 will utilize the rank 1 and rank 2 alternative futures for its examination while hypothetical scenario # 2 will use rank 2 and rank 3. The third hypothetical scenario will follow this same pattern with rank 2 and rank 4 alternative futures. This order was chosen based on the probability of each hypothetical scenario occurring as well as the likelihood of that specific alternative future applying to that type of scenario.
Hypothetical Scenario # 1 DHS Emphasizes the Possibility of Major Terrorist Attacks Due to Continued Uncooperative Behavior
Rank 1 and Rank 2 Comparison
Alternate Future Cooperation (C) + Cooperation (C): The DHS and the OAD (Other Agencies and Departments) become less competitive and more cooperative due to the potential disaster brought about by a terrorist attack that could have been prevented if the different agencies and departments had worked together.
The DHS and OAD becoming willing to commit towards cooperative behavior in the form of information sharing, joint operations, adherence to a leadership plan with the DHS at its helm and full disclosure of all activities pertaining to counter-terrorism. This situation manifests as a direct result of the realization that continued competition between the different departments results in a greater likelihood for international terrorists to recruit local Americans resulting in cases of domestic terrorism. This alternate future is characterized by the parties involved realizing the necessity of establishing shared goals regardless of previous sentiments that encouraged competitive behavior.
Alternate Future Cooperation and Competition (CCP) + Cooperation and Competition (CCP): The DHS is willing to cooperate with the different agencies and departments (ex: CIA, FBI, local law enforcement, etc.) involved despite the fact that the OAD has been limiting the amount of intelligence and cooperation extended to the DHS. The OAD is willing to do the same despite the DHS asserting its authority over their leadership structure. However, cooperation and information sharing in this case is limited.
Both the DHS and OAD want to prevent a terrorist attack from causing civilian deaths within the U.S. and, as such, become willing towards engaging towards more cooperative behavior. Despite this, there are still issues when it comes to the DHS assuming a leadership position and ordering around the different agencies and departments. Due to the lack of a clear-cut framework for operational leadership, the OAD views the actions of the DHS as being far too assertive resulting in uncooperative behavior and delays when it comes to information sharing and joint action. This creates a certain level of resentment on the part of the DHS and manifests in similar delays. In both parts of the spectrum, both the DHS and OAD are cooperating but the cooperation is marred due to organizational issues.
Hypothetical Scenario # 2 DHS seeks Executive and Congressional Interference
Rank 2 and Rank 3 Comparison
Alternate Future Cooperation and Competition (CCP) + Cooperation and Competition (CCP): The DHS and OAD are forced to cooperate due to Executive and Congressional Interference in their activities.
Under this alternative future, the constant uncooperative behavior between the DHS and OAD has become a cause for concern and has reached a point that direct intervention from congress becomes necessary. While both the DHS and OAD are still at odds and cooperation is unlikely to willingly occur, both the Executive and Congressional branches of the government are likely to implement a leadership body that consists of the department heads of the DHS and OAD. This has sufficient precedent in the past as evidenced by the formation of the DHS itself. In this future, the creation of a stable leadership body that is comprised of the different agencies is likely to help mitigate the uncooperative behavior resulting in better joint actions and information sharing. Thus, while still being somewhat competitive, both the DHS and OAD are cooperating far more effectively than they otherwise would have in the past.
Alternate Future Cooperation C + Competition (CP): the DHS would be willing to cooperate due to congressional oversight; however, the OAD would be furious since it would view the actions of the Executive and Congressional branches of government as impinging on its individual authorities.
In this case the DHS cooperates due to its perceived mandate in having to preventing terrorist actions from occurring within the U.S.; however, based on the work of Jenkins et al. (2011) it was noted that individual agencies and departments resent congressional and executive interference in their internal affairs and processes. As such, it is likely that cooperation between the DHS and OAD will be largely superficial with the OAD pursuing a more competitive set of actions rather than ones that foster cooperation.
Hypothetical Scenario # 3 Use of Soft Power
Rank 2 and Rank 4 Comparison
Alternate Future Cooperation and Competition (CCP) + Cooperation and Competition (CCP): Through the use of soft power the U.S. is able to foster better relations with other countries. Foreign nations are thus more likely to share information and contribute towards joint operations. There is still a level of competitive behavior due to slight distrust regarding the actions of the U.S.
Soft power tactics in this scenario has yielded positive benefits in the form of better cooperative behavior involving the U.S. and foreign countries. Realizing the necessity of cooperation, foreign nations capitulate towards the actions of the U.S. towards local intervention in its internal terrorist issues. This creates better international information networks to prevent the spread of terrorism and helps to foster more cooperation. However, based on the theory of realism, there is still a level of distrust between the U.S. and the other foreign countries resulting in some unilateral actions and information sharing and cooperation does have its limitations. Examples of this can be seen in the relation between Saudi Arabia and the U.S.
Alternate Future Cooperation (C) + Cooperation and Competition (CCP): The U.S. commits towards the use of soft power in order to help develop its relationship with other nations. This strategy is only partially effectively with countries still distrusting the U.S.
Under this alternative future the U.S. commits towards expanding its soft power program; however, it is only marginally effective with the different nations it engages in with such actions cooperating only to a certain extent. One example of this in action can be seen in the case of the relationship between Pakistan and the U.S. wherein the U.S. has contributed billions towards improving the armaments of the Pakistani government yet has only marginally been assisted when it comes to counter-terrorism operations.
LAMP Method STEP 9 to STEP 11
(STEP 9) Analyze each alternate future in terms of its consequences, (STEP 10) Determine focal events that could alter the relative probability, (STEP 11) Develop indicators for the events.
This section will examine the possible effects of the alternate futures on future challenges to homeland security. Aside from this, step 10 of this section will develop the focal events that are associated with such actions and the resulting indicators of such events will be created as well (step 11).
Hypothetical Scenario # 1 DHS Emphasizes the Possibility of Major Terrorist Attacks Due to Continued Uncooperative Behavior
Rank 1 and Rank 2 Comparisons
Alternate Future Cooperation (C) + Cooperation (C): The DHS and the OAD (Other Agencies and Departments) become less competitive and more cooperative due to the potential disaster brought about by a terrorist attack that could have been prevented if the different agencies and departments had worked together.
The consequences of this sort of scenario would be the creation of better cooperative behavior between the different agencies involved since their main driver would be a joint sense of responsibility over preventing attacks due to their uncooperative behavior. This would entail changes in organizational culture and how they would view information sharing and joint activities. The policy regime theory holds that in the policy world major attacks are rare and in most cases unpredictable; however, they do have huge effects. As such, in this possible future the DHS would emphasize the possible massive ramifications of the current problems plaguing the different agencies when it comes to cooperative behavior. It was seen in the aftermath of the September 11 attacks that there was a considerable level of cooperation and coordination between different departments due to the shared interests that such an event sparked between the different organizations. As such, given the current circumstance surrounding the potential for another large scale attack, it is likely that such a scenario would help to drive the DHS and other law enforcement agencies together to better combat a common threat. The long term consequences of this alternate future is the development of new organizational cultures and leadership councils whose specific purpose is foster information sharing and cooperation across the different agencies and departments.
Focal Events that could alter the relative probability
As explained in the literature review section, one of the main reasons behind the continued uncooperative behavior between the DHS and the OAD are the inherent budgetary constraints each entity is subject to. With budgetary allocations often being performance based, continued emphasis on individual agency performance regarding counter-terrorism activities as well as reduced budgets due to necessary budgets cuts would make the OAD less inclined towards cooperation with the DHS.
Key Indicators for Focal Events that could alter the relative probability
- Continued Budgetary allocations based on performance
- Reduced budgets for various agencies and departments
Alternate Future Cooperation and Competition (CCP) + Cooperation and Competition (CCP): The DHS is willing to cooperate with the different agencies and departments (ex: CIA, FBI, local law enforcement, etc.) involved despite the fact that the OAD has been limiting the amount of intelligence and cooperation extended to the DHS. The OAD is willing to do the same despite the DHS asserting its authority over their leadership structure. However, cooperation and information sharing in this case is limited.
The consequences of this alternate future are higher levels of cooperation between the DHS and the other agencies and departments involved; however, this level of cooperation is constrained due to internal organizational cultural differences. There will be better information sharing between the different departments but it will fairly limited and will not entail the different activities that a specific agency or law enforcement division has implemented in order to counter identified threats.
As mentioned in the literature review section of this study, overlapping command authorities and can create a considerable level of internal conflict when it comes to domestic counter-terrorism operations. This creates a situation where there is cooperation for the sake of responding to a perceived threat; however, the DHS would still be in conflict with the other agencies who perceive the interference of the DHS in their internal operations in a negative light. While there is no direct competition between the two parties due to shared interests, cooperation is still less than what it would ideally be.
Focal Events that could alter the relative probability
One of the possible focal events that could alter this relative probability would be changes in the internal organizational culture of the OAD resulting in a less competitive environment that is more inclined towards cooperation.
Key Indicators for Focal Events that could alter the relative probability
- Acceptance of outside leadership initiatives when it comes to counter-terrorist threats
- Greater levels of communication and association between different members of the DHS and OAD
Hypothetical Scenario # 2 DHS seeks Executive and Congressional Interference
Rank 2 and Rank 3 Comparisons
Alternate Future Cooperation and Competition (CCP) + Cooperation and Competition (CCP): The DHS and OAD are forced to cooperate due to Executive and Congressional Interference in their activities.
The consequences of this alternate future is only a marginally improved rate of cooperation and information sharing since the problems that have been elaborated on in this paper have not been addressed through this strategy. While executive and congressional interference may cause the DHS and other agencies to work closely together, it still does not address the underlying problems related to leadership issues, budgetary competition, overlapping responsibilities and local law enforcement agencies overstepping their mandates through abuse of the Patriot Act. As explained by Kiltz (2011), executive and congressional interference only superficially addresses the issues and does not address the inherent organizational issues that prevent the DHS and other agencies from cooperating with each other. The theory of cooperation and competition adds further credence to this assumption based on the fact that merely forcing the parties involved to cooperate does not resolve attitudes, perspectives, and the general willingness to actually perform proper methods of cooperation (Kiltz 2011, 7). The only way to do so would be to actually change the mindset of those involved into one that is more conducive towards cooperative behavior. This can only be accomplished through changes in the organizational culture that pervades the various agencies and departments involved in counter-terrorist operations. Thus, the long term consequence of this alternate future is likely a return to the previous status quo of uncooperative behavior.
Focal Events that could alter the relative probability
Addressing the problems related to leadership issues, budgetary competition, and overlapping responsibilities would be able to alter the relative probability and result in a case where the DHS and OAD are more likely to establish a highly cooperative and communicative relationship. Such an event would occur only if the DHS and the OAD actually willingly came together in order to develop a course of action that they could follow when it comes to counter-terrorism operations and authority rather than have it forced on them through an outside party.
Key Indicators for Focal Events that could alter the relative probability
- No budgetary competition between the different agencies
- No issues involving who leads the domestic counter-terrorism effort
- No organizational issues involving overlapping responsibilities
Alternate Future Cooperation (C) + Competition (CP): the DHS would be willing to cooperate due to congressional oversight; however, the OAD would be furious since it would view the actions of the Executive and Congressional branches of government as impinging on its individual authorities.
While cooperation between all parties involved would be ideal, it is unlikely to occur. As this paper has shown, there is a considerable level of mistrust between the various agencies resulting in a greater tendency for competitive rather than cooperative behavior. This is further compounded by the theory of cooperation and competition which lends further credence to the highly unlikely event of this occurring. In this alternate future, the DHS attempts to foster cooperation between itself and the other agencies within the U.S. due to pressure from Congress. However, despite its attempts to do so, other agencies that contribute towards the counter-terrorism effort are still under a competitive mindset. This prevents a proper cooperative relationship from being developed resulting in mismanaged efforts towards a unified front to prevent terrorist activities within the U.S.
Focal Events that could alter the relative probability
The main focal even that would help to alter the relative probability of this alternate future would be to remove the budgetary competition that is often the cause behind the uncooperative behavior between the different departments and agencies.
Key Indicators for Focal Events that could alter the relative probability
- Removal of performance based budgetary allocations
- Greater willingness to cooperate between the DHS and OAD
Hypothetical Scenario # 3 Use of Soft Power
Rank 2 and Rank 4 Comparisons
Alternate Future Cooperation and Competition (CCP) + Cooperation and Competition (CCP): Through the use of soft power the U.S. is able to foster better relations with other countries. Foreign nations are thus more likely to share information and contribute towards joint operations. There is still a level of competitive behavior due to slight distrust regarding the actions of the U.S.
The consequence of this action is the development of better intelligence ties between the U.S. and other foreign nations which would enable departments like the DHS to be able to track known terrorist threats and enter into joint actions with their international counterparts in order to arrest them. Do note though that relationships such as Cooperation (C) + Cooperation (C) is rarely if at all possible when it comes to cooperative agreements between different countries due to a combination of the disproportional relationships between more powerful and less powerful states. This is explained in the theory of realism and the lack of trust that manifests from this as indicated by the theory of cooperation and competition that creates a CPP (Cooperation – Competition + Cooperation – Competition) relationship between the two parties involved. In this situation there is cooperation between the two entities but it is still marred by the lack of trust by the smaller state towards the larger state. As such while there is still a level of mistrust between the U.S. and its foreign allies, it does allocate enough money to enhance the anti-terrorist capabilities of other countries (Walker 2007, 74). The increase in funding also targets all avenues of international cooperation to bolster new alliances and to create and sustain international networks that embrace information sharing. Thus, through this alternative future, while there is still a level of distrust between the two countries, there is at least a level of cooperation that ensures proper communication, collaboration and cooperation.
Focal Events that could alter the relative probability
One possible focal event that could alter the relatively probability would be if evidence shows that its foreign recipients of aid are actively hiding information that resulted in successful terrorist attack on the U.S. or are intentionally hiding information regarding known terrorists.
Key Indicators for Focal Events that could alter the relative probability
- Identification of willfully withholding information about terrorists and terrorist threats that resulted in attacks on U.S. soil
- Reduction/Removal of foreign aid programs to the country
- Accusations of withholding information that led to the death of U.S. citizens
Alternate Future Cooperation (C) + Cooperation and Competition (CCP): The U.S. commits towards the use of soft power in order to help develop its relationship with other nations. This strategy is only partially effectively with countries still distrusting the U.S.
In this alternate future, the relationship between states is oriented as C + CCP (Cooperation + Cooperation – Competition). The basis behind this ranking is due to studies such as those by Nieto-Gómez (2011) and Roberts (2011) which explained that due to U.S. interference in numerous international incidents, there are multiple terrorist groups that specifically want to target the U.S. The end result is that the U.S. becomes more willing to engage in cooperation with other countries in order to obtain information and detain these individuals; however, other countries are less likely to cooperate with such a desire. In this scenario, while these countries are willing to cooperate due to the potential dangers terrorists pose both in their country and abroad, they are unwilling to let the U.S. influence their domestic policy (this was elaborated on in the literature review section of the paper) as such, they are willing to cooperate only to a certain extent.
Focal Events that could alter the relative probability
Scaling back of U.S. interference in international affairs would result in greater trust for countries that are afraid of the growing influence of the U.S.
Key Indicators for Focal Events that could alter the relative probability
- Less involvement in international incidents
- Scaling back of money spent on international bases and fleets
Results of the Study
The results of the findings and analysis section revealed the following when it comes to addressing the homeland security issues that have been identified so far in this study:
- External Interference is necessary
- Differences in Organizational culture causes misunderstanding and strife
- Removal of performance based budgetary allocations
In this section, a step by step analysis of the revealed factors will be conducted in order to showcase the necessity of addressing them in order to facilitate a greater willingness to cooperate between the DHS and OAD.
Necessity of External Interference
The hypothetical scenarios have revealed that it is unlikely that the DHS and OAD within the U.S. would be able to develop a cooperative relationship of joint action and information sharing without some manner of external influence facilitating such a transition. The fact is that it is a combination of the lack of established inter-agency and inter-department protocols for leadership when it comes to counter-terrorist exercises that are at the heart of the issue. Simply put, the different agencies do not want to be controlled by a different department due to concerns over how it may impact their operations and individual mandates. As such, the findings and analysis section has shown that implementing some measure of external interference such as congressional or executive intervention is needed in order to properly bring about some form of effective internal changes. This is not to stay that the DHS and OAD are incapable of doing so themselves, in fact the study has showcased that they can develop the capacity for developing cooperation and communication between themselves; however, this would require the realization that their individual actions hurt rather than aid the counter-terrorism effort and, as such, is unlikely to occur.
Organizational Culture
Each of the different agencies and departments comprising the DHS and OAD are subject to their own internal protocols, internal operations, methods of leadership, etc. As such, this causes issues when it comes to developing any form of cooperative or communicative relationship since it is these differing organizational cultures and frameworks that cause a significant level of misunderstanding among the different departments. Forcing organizational change would be a terrible idea due to resistance to change from the different departments which would result in a drop in operational performance. Instead, it is advised that the development of some form of understanding and organizational exchange may be adopted wherein a liaison could be placed in each department/agency who is from another department/agency. This would help to facilitate better inter-agency/inter-department communication and collaboration since there would be someone from each department that would understand the nuances and intricacies inherent in each agency and help to better facilitate the process of cooperation.
Removal of performance based budgetary allocations
The inherent problem with the current budgetary situation for the different departments and agencies that are involved in counter-terrorist operations within the U.S. is that performance based budgetary allocations encourage competitive behavior. While it is understandable that in their inception this type of budgetary allocation was meant to increase the performance of the OAD, the fact remains that at the present it encourages agencies to withhold information or not participate in joint action due to how it may impact they capacity to perform better than other agencies. As such, by removing this type of allocation, this would encourage the OAD to cooperate fully with the DHS.
Strategies to impede future threats
The primary strategy is impudent leadership. Combining tools of soft power with selected hard power can transform the National Security apparatus greatly. Leadership is a common tool that the US has embraced for decades. The question is how this leadership has influenced matters of national security. From previous reviews, it is evident that the American leadership both at home and abroad has suffered poor coordination, thus leaving gaps for terrorists to exploit. Adopting the soft power model brings forth leadership styles that mobilize people with an objective and the leader helps the people in attaining those shared targets. It is time for the US leadership system to abandon the hierarchical leadership pyramid and shift to what Nye (2004, 106) refers to as leading from the center of a circle. The current leadership model in the DHS is a rigid one because information flow is often slow from top to the bottom or from bottom to the top. In addition, information is subject to distortion amid intended or unintended additions and omissions. The second model is more flexible because leaders at the center of the circle find it easy to coordinate large groups via persuasion and influence. Leaders are in a position to link straight to the subordinates, and thus their influence is felt on a wide scope. In a fast globalizing world, the US should ensure that it encourages leadership from the center since it is the way to impertinent leadership. The former Secretary of State, Hillary Clinton, echoed these sentiments by reaffirming the need to embrace civilian power in line with military power as essential pillars in enhancing global security.
The role of international training and cultural exchanges by the DHS can be a starting point in a bid to make a huge effect on both national and global security by utilizing soft tools as opposed to hard power. Given that the homeland security has a direct link to the global community, embracing intercultural literacy is paramount. Leadership in the homeland security has to understand the dynamics of culture. This aspect can enable them to act as pioneers of transformational leadership that motivates individuals from various diverse origins to fight global criminal cartels and ensure national security. These changes can only be possible if improvements are done on communication both within the DHS and within other agencies. Evidently, the homeland security has failed to speak a common language on various occasions, and thus increasing communication is necessary. Communication should not only focus on the security agencies, but also engage the public since security is everyone’s responsibility. The DHS should collaborate with learning institutions, media, and religious bodies to sensitize the public on terrorism. As the US adopts a new paradigm, civil rights and individual freedoms must be observed. Even though some risks have to be taken, this move will ensure that the process does not interfere with human dignity. The DHS in partnership with the media should embark on instilling trust in the public by keeping the society well informed with accurate and timely information (Caponi and Belmont 2015, 17).
Conclusion
Insufficient information sharing by key federal and international entities, overlapping responsibilities, differing organizational cultures and a highly bureaucratized system remain as the primary indicators of gaps in the US homeland security framework. Despite the mandate of the DHS to help coordinate the efforts of different agencies to combat threats to the security of the country, there is still a lack of interconnectedness between the different agencies which prevents coordinated efforts from being properly accomplished. It is based on this that this study has examined the factors that contribute to these issues and what methods could be implemented in order to mitigate them in the future. To accomplish this, this study utilized the LAMP methodology in order to examine the possible alternate futures when it comes to future challenges to homeland security are more likely to occur.
These alternate futures took into consideration the Deutsch and Coleman theory of cooperation and competition and thus the scenarios involved focused on either of the two aforementioned factors manifesting when it comes to inter-agency and inter-department cooperation and coordination. Utilizing the theory of competition and cooperation, it can be seen that the mindset surrounding these different agencies and departments is oriented more towards competition rather than cooperation with the challenge involving the future of Homeland Security being the necessity of shifting such a mindset away from competition and towards cooperation. Utilizing the LAMP methodology, several possible scenarios were created based on the theory of competition and cooperation wherein there is either cooperation, competition, both or neither and explained the basis behind each scenario and how likely any one of them is to occur based on what is currently known. The results of the findings and analysis section revealed the following when it comes to addressing the homeland security issues that have been identified so far in this study:
- External Interference is necessary
- Differences in Organizational culture causes misunderstanding and strife
- Removal of performance based budgetary allocations
By addressing these factors that were revealed in the findings and analysis section through an examination of the different future scenarios, the aforementioned challenges when it comes to homeland security within the U.S. can be addressed.
Do note though that some of the stringent measures adopted by the US Congress and the George Bush administration following the September 11 attacks have failed to impede security threats. Critiques posit that the bureaucratic measures have led to a string of security gaps even in the White House. To critics like Hummel, tight bureaucratic measures foster a circular sluggishness in decision-making. The policymakers have been reluctant to initiate a paradigm shift in security affairs. On the contrary, they keep on twisting old strategies to solve emergent problems. For instance, the DHS and the Secret Service require strong and flexible leadership, which is open to criticism and ready to share security information with relevant bodies. Working under strict bureaucracies is discouraging for workers and if it proves hard to avoid the protocols, then it is also difficult to enhance performance and coordination. Bureaucratic values discourage teamwork and decrease trust among security machinery, thus meaning that information sharing is minimal if any. This approach has proved inadequate particularly after the September 19, 2014 invasion of the White House by a stranger who managed to jump over the fence without being noticed.
After the September 11 attacks, homeland security has gained national interests with key projects focused toward promoting the safety of the US citizens. This review has established that the US Homeland Security faces many conceptual, structural, organizational, and functional problems that are posing threats to security. A review of several cases shows that even the White House has become vulnerable to attacks due to poor coordination and training of security agents. These dysfunctions have been directly linked to the lack of enough funding and rigid leadership that discourages innovation as well as employee motivation. Cultural diversity has also been identified as a possible problem impeding interagency cooperation. Consequently, this paper has predicted various challenges that ought to face the DHS including cyber attacks, biological weapons, nuclear weapons, and transnational crimes. The DHS in partnership with other bodies of the intelligence community has a chance to prevent these attacks from happening. As indicated earlier, the application of soft power is a major way forward since it does away with bureaucratic systems, whilst keeping the critical values of that system. However, through proper coordination and information sharing amongst security agencies, the US will stand a better position to promote homeland security.
Avenues for Future Research
One of the main limitations of this study was that it lacked the use of survey data from experts in the field regarding the possibility of particular actions occurring. The alternate futures that were utilized were based on the researcher’s examination of the literature review and the theory of competition and cooperation and, as such, are subject to personal interpretation. Using surveys in order to help gauge the likelihood of certain events would help to increase the overall accuracy of this study. Aside from this, further examination of the individual organizations themselves that were mentioned in this study could also be accomplished since what was done was a generalized overview rather than an in-depth individual examination.
Reference List
Agrell, Wilhelm. 2012. “The Next 100 Years? Reflections on the Future of Intelligence.” Intelligence and National Security 27, no. 1 (June): 118-132.
Bajorek, Jennifer. 2005. “The Offices of Homeland Security,or, Hölderlin’s Terrorism.” Critical Inquiry 31, no. 4: 874-902.
Barnett, Thomas P. M., and Henry H. Gaffney Jr. 2005. “Global Transaction Strategy.” Institute Of Public Affairs Review 57, no. 1: 18.
Barry, Tom. 2009. “The New Political Economy of Immigration.” Dollars & Sense no. 280: 28.
Bjelopera, Jerome P. 2015. “Sifting Domestic Terrorism from Other Illegal Activity.” Congressional Research Service: Report 1-3.
Bolkcom, Christopher, and Blas Nuñez-Neto. 2008. “Homeland Security: Unmanned Aerial Vehicles and Border Surveillance.” Congressional Research Service: Issue Brief 1-6.
Busch, Nathan E., and Austen D. Givens. 2012. “Public-Private Partnerships in Homeland Security: Opportunities and Challenges.” Homeland Security Affairs 8, 1-23.
Caponi, Steven, and Kate Belmont. 2015. “Maritime Cybersecurity: A Growing Threat Goes Unanswered.” Intellectual Property & Technology Law Journal 27, no. 1 (January): 16-18.
Caruson, Kiki. 2004. “Mission Impossible? The Challenge of Implementing an Integrated Homeland Security Strategy.” Journal Of Homeland Security & Emergency Management 1, no. 4: 1-22.
Champion, Christopher. 2005. “The Revamped FISA: Striking a Better Balance between the Government’s Need to protect itself and the fourth amendment.” Vanderbilt Law Review 58, no. 5 (October): 1671-1703.
Clauser, Jerome, and Jan Goldman. 2008. An Introduction to Intelligence Research and Analysis. Lanham: Scarecrow Press.
Davis, Lois. 2010. Long-Term Effects of Law Enforcement’s Post-9/11 Focus on Counterterrorism and Homeland Security. Santa Monica, CA: RAND Corporation.
Davis, Charles N., and Michelle Albert. 2011. “Using secrecy to fight terrorism? Access, homeland security, and the ‘mosaic theory’ as a rationale for closure.” Continuum: Journal Of Media & Cultural Studies 25, no. 2: 251-259.
Dawson, Jim. 2002. “Science and Technology Are a Focus of Debate on New Homeland Security Department.” Physics Today 55, no. 8: 22.
Dickens, J. J. 2007. “DHS: U.S. Department of Homeland Security.” Choice: Current Reviews For Academic Libraries 44, no. 12: 2179.
Dodsworth, Francis. 2012. “Criminologists on Terrorism and Homeland Security.” Contemporary Sociology 41, no. 5: 628-629.
Dohrn, Bernardine. 2003. “Homeland Imperialism: Fear and Resistance.” Monthly Review: An Independent Socialist Magazine 55, no. 3: 130.
Dolnik, Adam. 2013. Conducting terrorism field research: A guide. Oxford: Routledge.
Donahue Jr., Donald A., Stephen O. Cunnion, Carey D. Balaban, and Ken Sochats. 2010.
“Meeting Educational Challenges in Homeland Security and Emergency Management.” Journal Of Homeland Security & Emergency Management 7, no. 1: 1-12.
Filiol, Eric. 2013. “The Control of Technology by Nation State: Past, Present and Future: The Case of Cryptology and Information Security.” Proceedings Of The European Conference On Informations Warfare & Security 62-69.
Friedrich, Nancy. 2005. “Technology Fills Homeland-Security Gaps.” Microwaves & RF 44, no. 6: 33-84.
Friedman, Benjamin. 2011. “Managing Fear: The Politics of Homeland Security.” Political Science Quarterly 126, no. 1 (May): 77-110.
George, Justin. 2010. “Review of Is America Safe? Terrorism, Homeland Security, and Emergency Preparedness.” Journal Of Homeland Security & Emergency Management 7, no. 1: 1-4.
Gorman, Siobhan. 2004. “On Guard, But How Well? (Cover story).” National Journal 36, no. 10: 696-703
GREENER, BETH. 2013. “ILLUMINATING THE DARK ARTS OF WAR: Terrorism, Sabotage and Subversion in Homeland Security and the New Conflict.” New Zealand International Review 38, no. 2: 30-31
Goldstein, Mark. 2013. “Homeland Security: Federal Protective Service Continues to Face Challenges with Contract Guards and Risk Assessments at Federal Facilities: Testimony Before the Committee on Homeland Security and Governmental Affairs, U.S. Senate.” United States Government Accountability Office. Web.
Guest, Gregory, Emily Namey, and Marilyn Mitchell. 2012. Collecting Qualitative Data: A Field Manual for Applied Research. Thousand Oaks: Sage Publications.
Hammond, Andrew. 2008. “Two countries divided by a common threat? International perceptions of US and UK counter-terrorism and homeland security responses to the
post-September 2001 threat environment.” Place Branding & Public Diplomacy 4, no. 3: 218-239.
Hennink, Monique. 2014. Focus Group Discussions. Oxford: Oxford University Press.
Hessman, James D. 2003. “Congress, President Face a Year of Decision In National Security and Homeland Defense.” Sea Power 46, no. 2: 9.
Hill, Joshua, Willard M. Oliver, and Nancy E. Marion. 2010. ““Shaping history” or “Riding the wave”?: President Bush’s influence on the public opinion of terrorism, homeland security, & crime.” Journal Of Criminal Justice 38, no. 5: 896-902.
Honig, Arthur. 2007. “A new direction for theory-building in intelligence studies.” International Journal of Intelligence and Counter Intelligence 20, no. 4 (August): 699-716.
Hymans, Jacques. 2006. “Theories of nuclear proliferation: The state of the field.” Nonproliferation Review 13, no. 3 (May): 455-465.
Jenkins, Brian, Andrew Liepman, and Henry Willis. 2014. Identifying Enemies among Us: Evolving Terrorist Threats and the Continuing Challenges of Domestic Intelligence Collection and Information Sharing. Santa Monica, CA: Rand.
Johnson, Branden B. 2010. “Trust and Terrorism: Citizen Responses to Anti-Terrorism Performance History.” Risk Analysis: An International Journal 30, no. 9: 1328-1340.
Jones, Keith C., and L. Milton Glisson. 2009. “HOMELAND SECURITY VS. CABOTAGE: ISSUES OF TERRORISM OR PLOYS.” Journal Of Transportation Management 20, no. 1: 35-47.
Josselson, Ruthellen. 2013. Interviewing for Qualitative Inquiry: A Relational Approach. New York: The Guilford Press.
Kamien, David. 2006. The McGraw-Hill Homeland Security Handbook. New York, NY: McGraw-Hill.
Kapucu, Naim. 2008. “Review of Introduction to Homeland Security: Understanding Terrorism with an Emergency Management Perspective.” Journal Of Homeland Security & Emergency Management 5, no. 1: 1-5.
Karl, Bob. 2011. “Reduce risk: Consider SAFETY Act designation.” Nonprofit Business Advisor no. 260: 1-2.
Kiltz, Linda, and James D. Ramsay. 2012. “Perceptual Framing of Homeland Security.” Homeland Security Affairs 8, no. 1: 1-26.
Kiltz, Linda. 2011. “The Challenges of Developing a Homeland Security Discipline to Meet Future Threats to the Homeland.” Journal Of Homeland Security & Emergency Management 8, no. 2: 1-20.
Khalid, Iram, and Marium Kamal. 2015. “The Homeland Security Initiatives for Pakistan: A Grand Strategy.” South Asian Studies 30, no. 1: 15-36.
LaPira, Timothy. 2014. “Lobbying after 9/11: Policy Regime Emergence and Interest Group Mobilization.” The Policy Studies Journal 42, no. 2 (June): 226-251.
Lieven, Anatol, and John Hulsman. 2006. Ethical Realism: A Vision for America’s Role in the World. New York, NY: Pantheon Books.
Light, Paul. 2007. “The Homeland Security Hash.” Wilson Quarterly 31, no. 2: 36-44.
Marion, Nancy, and Kelley Cronin. 2009. “Law Enforcement Responses to Homeland Security Initiatives: The Case of Ohio.” Southwest Journal of Criminal Justice 6, no. 1 (May): 4-24.
Marshall, Catherine, and Gretchen Rossman. 2010. Designing Qualitative Research. Thousand Oaks: Sage Publications.
Maxwell, Bruce. 2004. Homeland Security: A Documentary History. Washington, D.C.: CQ Press, 2004.
May, Peter, Ashley Jochim, and Joshua Sapotichne. 2011. “Constructing Homeland Security: An Anemic Policy Regime.” Policy Studies Journal 39, no. 2 (May): 285-307.
May, Peter J., Joshua Sapotichne, and Samuel Workman. 2009. “Widespread Policy Disruption: Terrorism, Public Risks, and Homeland Security.” Policy Studies Journal 37, no. 2: 171-194.
May, Peter J., Samuel Workman, and Blyan D. Jones. 2008. “Organizing Attention: Responses of the Bureaucracy to Agenda Disruption.” Journal Of Public Administration Research & Theory 18, no. 4: 517-541.
Maurer, David C., and Charles Michael Johnson Jr. 2013. “DHS Should Take Action to Better Ensure Resources Abroad Align with Priorities.” GAO Reports 1-71.
McCreight, Robert. 2009. “Educational Challenges in Homeland Security and Emergency Management.” Journal Of Homeland Security & Emergency Management 6, no. 1: 1-6
Moran, Christopher, 2011. “Intelligence and the Media: The press, government secrecy and the ‘Buster’ Crabb Affair.” Intelligence and National Security 26, no. 5 (October): 676-700.
Moss, Mitchell, Charles Schellhamer, and David A. Berman. 2009. “The Stafford Act and Priorities for Reform.” Journal Of Homeland Security & Emergency Management 6, no. 1: 1-21
Mumpower, Jeryl L., Liu Shi, James W. Stoutenborough, and Arnold Vedlitz. 2013.
“Psychometric and Demographic Predictors of the Perceived Risk of Terrorist Threats and the Willingness to Pay for Terrorism Risk Management Programs.” Risk Analysis: An International Journal 33, no. 10: 1802-1811.
Murray, Williamson. 2003. National Security Challenges for the 21st Century. Carlisle, PA: Strategic Studies Institute, U.S. Army War College.
Nakaya, Andrea. 2005. Homeland Security. Detroit, MI: Greenhaven Press.
Nieto-Gómez, Rodrigo. 2011. “The Power of “the Few”: A Key Strategic Challenge for the Permanently Disrupted High-Tech Homeland Security Environment.” Homeland Security Affairs 7, no. 1: 2-22.
Nieto-Gómez, Rodrigo. 2011. “Preventing the Next 9/10: The Homeland Security Challenges of Technological Evolution and Convergence in the Next Ten Years.” Homeland Security Affairs 7, no. 2: 1-6.
Nye, Joseph. 2004. Soft Power: The Means to Success in World Politics. New York, NY: Public Affairs.
Omand, David. 2012. “Into the Future: A Comment on Agrell and Warner.” Intelligence and National Security 27, no. 1(November): 154-156.
Ortiz, Christopher W., Nicole J. Hendricks, and Naomi F. Sugie. 2007. “Policing Terrorism: The Response of Local Police Agencies to Homeland Security Concerns.” Criminal Justice Studies 20, no. 2: 91-109
Packer, Martin. 2011. The Science of Qualitative Research. Cambridge: Cambridge University Press.
Pantucci, Raffaello. 2007. “Homeland Security in the UK.” Military Technology 31, 3-5.
Patton, Michael. 2010. Qualitative Research & Evaluation Methods. Thousand Oaks: Sage.
Patton, Michael. 2014. Qualitative Research & Evaluation Methods: Integrating Theory and Practice. Thousand Oaks: Sage.
Puyvelde, Damien. (2013) “Intelligence Accountability and the role of public interest groups in the United States.” Intelligence and National Security 28, no. 2 (May): 139-158.
Persell, Deborah J., and Susan Speraw. 2008. “Toward a Theory of Homeland Security Nursing.” Journal Of Homeland Security & Emergency Management 5, no. 1: 1-15
Prunckun, Hank. 2014. Scientific Methods of Inquiry for Intelligence Analysis Blue Ridge Summit: Rowman & Littlefield Publishers.
RAMÍREZ PARTIDA, HÉCTOR R. 2014. “Post-9/11 U.S. Homeland Security Policy Changes and Challenges: A Policy Impact Assessment of the Mexican Front.” Norteamérica: Revista Académica Del CISAN-UNAM 9, no. 1: 55-78.
Richelson, Jeffrey. 2010. The US Intelligence Community. Boulder: Westview Press.
Ritchey, Diane. 2011. “Proud To Be Security: How Roles Changed After 9/11.” Security: Solutions For Enterprise Security Leaders 48, no. 9: 38-50.
Roberts, Mark J. 2011. “Terrorism and Homeland Security: Perspectives, Thoughts, and Opinions.” Journal Of Strategic Security 4, no. 3: 69-72.
Robinson, Scott, Liu Xinsheng, James Stoutenborough, and Arnold Vedlitz. 2013.
“Explaining Popular Trust in the Department of Homeland Security.” Journal of Public Administration Research & Theory 23, no. 3 (June): 713-733.
Rogers, Christopher. 2014. “A Slow March Towards Thought Crime: How The Department of Homeland Security’s Fast Program Violates the Fourth Amendment.” American University Law Review 64, no. 1 (December): 335-337.
Rychnovska, Dagmar. 2014. “Securitization and the Power of Threat Framing.” Perspectives: Central European Review of International Affair 22, no. 2: 9-31.
Saller, Mark, and Can Mutlu. 2012. Research Methods in Critical Security Studies: An Introduction. Oxford: Routledge.
Schmid, Alex. 2013. The Routledge handbook of terrorism research. Oxford: Routledge.
Schimmel, Kimberly S. 2012. “Protecting the NFL/ militarizing the homeland: Citizen soldiers and urban resilience in post-9/11 America.” International Review For The Sociology Of Sport 47, no. 3: 338-357.
Schneider, Kent R. 2013. “Teamwork Defines Homeland Security Success.” Signal 67, no. 6: 17.
Schollmeyer, Josh. 2005. “HOMELAND SECURITY: Terrorism takes a holiday.” Bulletin Of The Atomic Scientists 61, no. 4: 8.
Shear, Michael, and Michael Schmidt. 2014. “Armed Intruder at White House Got to East Room.” The New York Times. Web.
Shepherd, Laura. 2012. Critical Approaches to Security: An Introduction to Theories and Methods. Oxford: Routledge.
Sigfrinius, Gary. 2005. “Terrorism…In Minnesota?.” Minnesota Fire Chief 42, no. 1: 14.
Silverman, David. 2001. Interpreting qualitative data: methods for analyzing talk, text, and interaction. Thousand Oaks: Sage.
Sparks, Thomas, and Glenn Sulmasy. 2006. International Law Challenges: Homeland Security and Combating Terrorism. Newport, R.I.: Naval War College.
Stana, Richard. 2003. Homeland Security Challenges to Implementing the Immigration Interior Enforcement Strategy. Washington, D.C: U.S. General Accounting Office.
Thachuk, Kimberley. 2007. Transnational Threats: Smuggling and Trafficking in Arms, Drugs, and Human Life. Westport, CT: Praeger.
Walker, David. 2007. Homeland Security Management and Programmatic Challenges Facing the Department of Homeland Security: Testimony Before the House Homeland Security Committee. Washington, D.C: U.S. Government Accountability Office.
Warner, Michael. 2012. “Reflections on Technology and Intelligence Systems.” Intelligence and National Security 27, no. 1: 133-153.
Waugh, William L. 2003. “Terrorism, Homeland Security and the National Emergency Management Network.” Public Organization Review 3, no. 4: 373-385.
White, Stanley I. 2010. “Moving From Mindset To Outcome.” Journal Of Counterterrorism Homeland Security International 16, no. 3: 48-51.
Zimmerman, Peter D. 2011. “Science since 9/11: Homeland insecurity.” Nature 477, no. 7363: 153-154.