What does the data link layer do?
The data link layer offers the functional and procedural way for the transmission of data between network entities and to detection and correction errors that may occur in the physical layer (Fitzgerald & Dennis, 2001). Typically, the data link layer was planned for point-to-point and point-to-multipoint media, characteristic of wide-area media in the telephone system (Stallings, 1998). This was because LAN architecture, which included broadcast-capable multi-access media, was developed independently of the ISO work, which only assumed sub layering and management functions not required for WAN use (Stallings, 1998).
In today’s practice, only error detection, not flow control using a sliding window, is present in modern data link protocols such as Point-to-Point Protocol and, on local area networks, the LLC layer is not used for most protocols on Ethernet, and, on other local area networks, its flow control and acknowledgment mechanisms are rarely used (Stallings, 1998). Sliding window flow control and acknowledgment are used at the transport layers by protocols such as TCP but are still used in niches where X.25 offers performance advantages (Fitzgerald & Dennis, 2001).
Both WAN and LAN services arrange bits, from the physical layer, into logical sequences called frames but not all physical layer bits necessarily go into frames, as some of these bits are purely intended for physical layer functions (Fitzgerald & Dennis, 2001).
Connection-oriented WAN data link protocols, in addition to framing, detect and may correct errors and are capable of controlling the rate of transmission (Stallings, 1998). A WAN data link layer might implement a sliding window flow control and acknowledgment mechanism to provide reliable delivery of frames; that is the case for SDLC and HDLC, and derivatives of HDLC such as LAPB and LAPD (Stallings, 1998).
Practical, connectionless LANs began with the pre-IEEE Ethernet specification, and this layer manages the interaction of devices with a shared medium, which is the function of a Media Access Control sub-layer (Stallings, 1998).
Under what circumstances is forward error correction desirable?
In practice, forward error correction (FEC) is a structure of error control for data transfer, in which the sender adds redundant data to its messages, also referred to as an error correction code (Fitzgerald & Dennis, 2001). This is to allow the receiver to sense and correct errors without the need to ask the sender for additional data (Fitzgerald & Dennis, 2001). The benefit of forwarding error correction is that a back-channel is not required, or that retransmission of data can often be avoided, at the cost of higher bandwidth requirements on average (Fitzgerald & Dennis, 2001). Forward error correction is therefore applied in situations where retransmissions are relatively costly or impossible (Fitzgerald & Dennis, 2001).
Forward error correction devices are normally situated near the receiver of an analog signal, in the first stage of digital processing after a signal has been received Implying error correction devices circuits are often an integral part of the analog-to-digital conversion process, also involving digital modulation and demodulation, or line coding and decoding (Stallings, 1998). Most Forward error correction coders can as well produce a bit-error-rate signal which can be used as feedback to fine-tune the analog receiving electronics (Stallings, 1998). Further, forward error correction detection algorithms, such as the soft Viterbi algorithm, can take analog data in, and generate digital data on output (Stallings, 1998). The maximum fraction of errors that can be corrected is determined in advance by the design of the code, so different forward error-correcting codes are suitable for different conditions (Stallings, 1998).
What does the network layer do?
The network layer provides the functional and procedural means of transferring variable length data sequences from a source to a destination via one or more networks while maintaining the quality of service requested by the Transport layer (Boggs et al, 1988). The Network layer performs network routing functions, and might also perform fragmentation and reassembly, and report delivery errors (Boggs et al, 1988). Routers operate at this layer, by sending data throughout the extended network and making the Internet possible (Boggs et al, 1988). Therefore, this is a logical addressing scheme whereby values are chosen by the network engineer (Boggs et al, 1988).
The most popular example of a layer 3 protocol is the Internet Protocol (IP) which manages the connectionless transfer of data one hop at a time, from end system to ingress router, to router to router, and from egress router to destination end system (Stallings, 1998). The network layer is not responsible for reliable delivery to the next hop, but only for the detection of error packets so they may be discarded (Stallings, 1998). When the medium of the next-hop cannot accept a packet in its current length, IP is responsible for fragmenting into sufficiently small packets that the medium can accept it (Stallings, 1998).
Compare and contrast bridges, routers, and gateways
Bridges
In practice a bridge reads the outermost section of data on the data packet, to tell where the message is going and thus reducing the traffic on other network segments since it does not send all packets (Fitzgerald & Dennis, 2001). Bridges can be programmed to reject packets from particular networks (Fitzgerald & Dennis, 2001). Bridging occurs at the data link layer of the OSI model, which means the bridge cannot read IP addresses, but only the outermost hardware address of the packet (Fitzgerald & Dennis, 2001).
Bridges forward all broadcast messages and only a special bridge called a translation bridge will allow two networks of different architectures to be connected (Fitzgerald & Dennis, 2001). Bridges do not normally allow the connection of networks with different architectures. In Transparent Bridging a bridging table is built as they receive packets. Therefore, if the address is not in the bridging table, the packet is forwarded to all segments other than the one it came from (Stallings, 1998).
Routers
A router is used to route data packets between two networks in which it reads the information in each packet to tell where it is going (Fitzgerald & Dennis, 2001). If it is destined for an immediate network it has access to, it will strip the outer packet, readdress the packet to the proper ethernet address, and transmit it on that network (Fitzgerald & Dennis, 2001). If it is destined for another network and must be sent to another router, it will re-package the outer packet to be received by the next router and send it to the next router (Fitzgerald & Dennis, 2001). Routers can connect networks with different architectures such as Token Ring and Ethernet however they can transform information at the data link level, routers cannot transform information from one data format such as TCP/IP to another such as IPX/SPX (Stallings, 1998). Routers do not send broadcast packets or corrupted packets (Stallings, 1998). If the routing table does not indicate the proper address of a packet, the packet is discarded (Stallings, 1998).
Gateway
A gateway can translate information between different network data formats or network architectures (Fitzgerald & Dennis, 2001). It can translate TCP/IP to AppleTalk so computers supporting TCP/IP can communicate with Apple brand computers (Fitzgerald & Dennis, 2001). Most gateways operate at the application layer but can operate at the network or session layer of the OSI model (Fitzgerald & Dennis, 2001).
Gateways will start at the lower level and strip information until it gets to the required level and repackage the information and work its way back toward the hardware layer of the OSI model (Fitzgerald & Dennis, 2001). To confuse issues, when talking about a router that is used to interface to another network, the word gateway is often used whereby this does not mean the routing machine is a gateway as defined here, although it could be (Fitzgerald & Dennis, 2001).
Under what circumstances would you want to use a multiprotocol router?
Circumstances I would want to use a multiprotocol router are where I would like to support two or more communications protocols, such as IP and IPX. Further, multiprotocol is used to switch network traffic between different LANs located throughout the enterprise as well as to switch LAN traffic to WANs (Boggs et al, 1988).
Case Study
Introduction
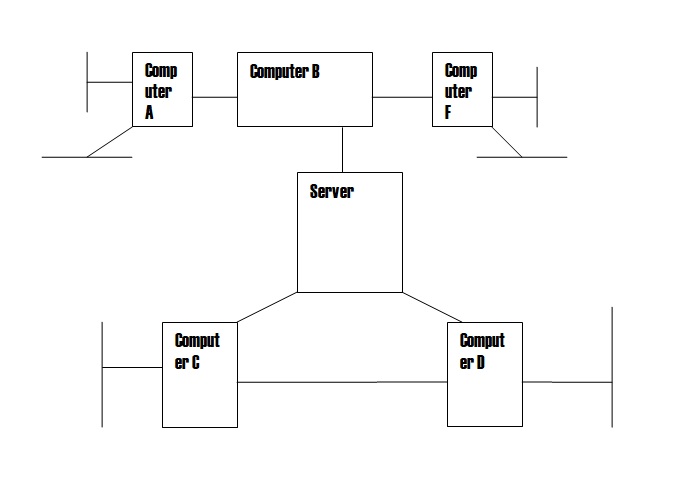
A Local Area Network (LAN) connects machines in close geographical proximity and a Wide Area Network (WAN) is used for networks that expand beyond the department or office, for instance, the Internet is a collection of networks acting as one (Fitzgerald & Dennis, 2001). Usually, a WAN will have one or more slow links, perhaps over telephone lines between cities, whereas all the links in a LAN will be fast (Fitzgerald & Dennis, 2001). This difference in speed is important for optimizing the overall network performance. If the international service division employs LAN, it is expected to share files, programs, or printers, all without being particularly aware of where the physical resources we’re using are located. LANs providing these types of services are typically set up either as “peer-to-peer” or “dedicated-server” LANs or perhaps as a combination of the two (Fitzgerald & Dennis, 2001).
The international service division should use Peer-to-peer LANs. This is because all the machines on a peer-to-peer LAN are equal (Fitzgerald & Dennis, 2001). Further, as long as the file’s owners give permission, a file on machine A can be accessed from machine B, and vice versa (Fitzgerald & Dennis, 2001). Peer-to-peer LANs do not require anyone’s machine to be a dedicated, high-performance server; service by a peer-to-peer LAN is often cheaper for this reason (Fitzgerald & Dennis, 2001).
Further, Peer-to-peer LANs work well when only a small number of machines are connected to them however as the size of the LAN grows, peer-to-peer services can become quite disorganized, and because each machine on the LAN must be powerful enough to serve all of its peers, the cost increases and therefore for larger LANs, the dedicated client-server LAN architecture becomes more cost-effective.
Discussion
The type of LAN they should install is Ethernet. This is because Ethernet is a family of frame-based computer networking technologies for local area networks (LANs) (Stallings, 1998). It defines some wiring and signaling standards for the physical layer, through means of network access at the Media Access Control (MAC)/Data Link Layer, and a common addressing format (Boggs et al, 1988). Ethernet is standardized as IEEE 802.3 and the combination of the twisted pair versions of Ethernet for connecting end systems to the network, along with the fiber optic versions for site backbones, is the most widespread wired LAN technology (Boggs et al, 1988). In recent years, Wi-Fi, the wireless LAN standardized by IEEE 802.11, is prevalent in home and small office networks and augmenting Ethernet in larger installations (Boggs et al, 1988)
LAN network bottlenecks
Bottlenecks occur on a system when one or more devices become constrained (). The devices’ monitor detects the constraint, and performance analysis indicates a bottleneck (Stallings, 1998). When an individual is assigned to check periodically for bottlenecks or generate a report, the performance-analysis function looks for bottlenecks in managed-system hardware performance (Stallings, 1998). When one or more performance-analysis monitors meet or exceed their preset threshold settings and you have selected Generate Bottleneck events during report definition, a bottleneck event is generated. When the performance-analysis function detects a bottleneck, it diagnoses the problem and determines a potential solution (Stallings, 1998).
Multiple bottlenecks can occur, for example, if a disk bottleneck and a memory bottleneck can occur concurrently, then the bottleneck becomes a disk + memory bottleneck (Fitzgerald & Dennis, 2001). The recommendation for addressing a bottleneck with two devices may not be the same as addressing two bottlenecks individually (Fitzgerald & Dennis, 2001). In the case of a disk + memory bottleneck, the performance-analysis algorithm recognizes that insufficient memory can lead to disk thrashing, so the recommendation is to add more memory and leave the disk drives unchanged (Fitzgerald & Dennis, 2001). Because devices often interact in this way, each combination of device types (for example, processor, memory, disk, and LAN adapter) constitutes a separate bottleneck with its recommendation (Fitzgerald & Dennis, 2001).
Latent bottlenecks
Often when you have one bottleneck, others are not evident while the system is slowed by the first bottleneck (Stallings, 1998). The bottleneck that is currently happening is realized, but one that is not evident while the system is slowed is a latent bottleneck (Stallings, 1998). It is also possible for a given device to contribute to a latent bottleneck for part of the time and to a realized bottleneck for part of the time (Stallings, 1998).
Forecasted bottlenecks
The performance-analysis algorithm scans for bottlenecks on each system (Stallings, 1998). If no bottlenecks are found for a given system, then performance analysis uses a forecasting algorithm to look at all the system monitors simultaneously to predict what bottlenecks might occur and report the first bottleneck that it foresees. (Stallings, 1998) The forecast period is the same length as the reporting period, for example, a reporting period of one month can have a forecast of one month into the future (Stallings, 1998).
LAN safeguards
Today’s stand-alone systems and network servers, with online mass-storage capacities of several gigabytes, require high-capacity backup and archiving subsystems (Boggs et al, 1988). For many businesses, the primary objective of backing up data is to guard against data loss. In the long run, however, the finite capacity and no removable nature of desktop systems’ hard drives put secondary storage right up there with death and taxes–it’s a must (Boggs et al, 1988).
Several types of streaming-tape recording media continue to be the backbone of computer backup and archiving for the LAN market (Boggs et al, 1988). Since the early 1980s, QIC tape drives have dominated secondary storage solutions for stand-alone systems and LANs (Boggs et al, 1988).
Further to prevent theft of software, many programs are now available with serial numbers whereby it very difficult to crack them without the
References
Boggs, D.R., Mogul, J.C., and Kent, C.A. (1988). “Measured capacity of an Ethernet: myths and reality”. ACM SIGCOMM Computer Communication Review 18 (4): 222–234. ACM Press.
Fitzgerald & Dennis (2001). Business Data Communications and Networking. John Wiley & Sons.
Stallings, William Richard (1998). The Origins of OSI Prentice Press.